What is Anomaly-Based IDS Algorithm
An Anomaly-Based Intrusion Detection System (IDS) Algorithm is a cybersecurity technique used to detect unusual patterns or behaviors in a network or system. Unlike signature-based IDS, which relies on known attack patterns, anomaly-based IDS identifies deviations from normal behavior. These deviations, also called anomalies, may indicate potential cyber threats such as malware, insider attacks, or zero-day exploits. The core idea behind this algorithm is to establish a baseline of normal system activity and continuously monitor incoming data to detect any abnormal changes. If the system detects behavior that significantly deviates from this baseline, it raises an alert for further investigation. Anomaly-based IDS algorithms are particularly powerful because they can detect previously unknown attacks, making them essential in modern cybersecurity frameworks.
Introduction of Anomaly-Based IDS Algorithm
With the rapid growth of digital systems and increasing sophistication of cyberattacks, traditional security methods are no longer sufficient. Signature-based detection systems struggle to identify new or evolving threats because they rely on predefined attack signatures. This limitation led to the development of anomaly-based IDS algorithms. These systems focus on understanding what “normal” behavior looks like within a system and identifying any deviations from that norm. Anomaly-based IDS uses techniques from machine learning, statistics, and artificial intelligence to build behavioral models. These models are then used to monitor system activity in real time.
Key characteristics include:
- Detection of unknown threats
- Adaptive learning capabilities
- Continuous monitoring
- Reduced dependency on signature databases
However, these systems may produce false positives if normal behavior changes frequently, making proper tuning and training essential.
Detailed Anomaly-Based IDS Algorithm with Steps and Formulas
The Anomaly-Based IDS algorithm consists of several structured steps:
Step 1: Data Collection
The system collects network or system data such as:
- Packet size
- Traffic volume
- Login attempts
- CPU usage
- System calls
Let the dataset be represented as:
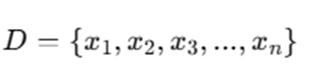
where each xi represents a data point or feature vector.
Step 2: Feature Extraction
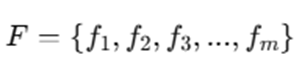
Relevant features are extracted from raw data.
Each feature represents a measurable property such as:
- Number of connections per second
- Average packet size
- Protocol type
Step 3: Normal Profile Creation
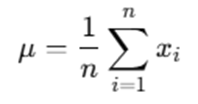
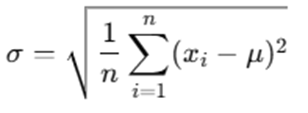
The system builds a baseline model of normal behavior.
Mean (average):
Standard deviation:
Step 4: Model Training
Machine learning or statistical models are trained using normal data.
Examples:
- Gaussian Model
- k-means clustering
- Neural networks
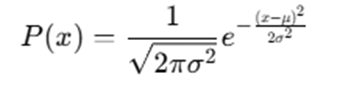
For Gaussian distribution:
Step 5: Monitoring Incoming Data
New data points xnew are continuously monitored and compared with the baseline.
Step 6: Anomaly Detection
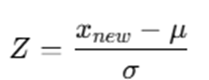
Calculate anomaly score:
If:
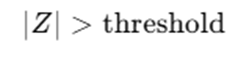
then the data is considered anomalous.
Step 7: Alert Generation
If anomaly is detected:
- Generate alert
- Log event
- Trigger response mechanism
The anomaly-based IDS algorithm begins by collecting large volumes of system or network data, which may include user activities, network packets, or system logs. This data is then processed to extract meaningful features that represent system behavior. These features play a critical role in determining what constitutes normal activity. Once the relevant features are identified, the system builds a normal behavior profile using statistical methods such as mean and standard deviation. This baseline represents how the system typically operates under normal conditions. Next, the algorithm trains a model using historical data. This model could be based on statistical distributions or machine learning techniques, depending on the complexity of the system. The purpose of this model is to learn patterns of normal behavior. After training, the system continuously monitors incoming data in real time. Each new data point is evaluated against the established baseline. The algorithm calculates an anomaly score, often using a Z-score or probability function, to determine how far the new data deviates from normal behavior. If the deviation exceeds a predefined threshold, the system flags the activity as suspicious. Finally, the IDS generates an alert, which can be used by security teams to investigate and respond to potential threats.
Example of How Anomaly-Based IDS Algorithm Works
To understand how an Anomaly-Based IDS Algorithm works in practice, let’s break down the scenario step by step with deeper clarity.
Scenario Overview
Assume a network monitoring system observes login activity over time and builds a normal behavior profile based on historical data.
- Average login attempts per minute (mean, μ) = 5
- Standard deviation (σ) = 2
This means that under normal conditions, the number of login attempts typically falls within a predictable range around 5.
Step 1: Understanding Normal Behavior
In statistics, most normal values lie within a certain range:
- Normal range ≈ μ ± 2σ
- So here:
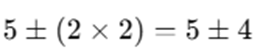
→ Normal range = 1 to 9 login attempts per minute
Any value within this range is generally considered normal behavior.
Step 2: Observing New Activity
Now, the IDS observes a sudden spike:
- New login attempts = 15 per minute
This is significantly higher than the normal range (1–9), so the system proceeds to calculate how abnormal this value is.
Step 3: Calculating the Z-Score
The Z-score measures how far a value deviates from the mean in terms of standard deviations.
z=5
Step 4: Interpreting the Z-Score
A Z-score of 5 means:
- The observed value (15 login attempts) is 5 standard deviations above the mean
- In a normal distribution, values beyond ±3 standard deviations are extremely rare (less than 0.3% probability)
So:
- Z ≤ 2 → Normal behavior
- 2 < Z ≤ 3 → Suspicious
- Z > 3 → Highly anomalous
Here, Z = 5, which is far beyond the acceptable threshold.
Step 5: Anomaly Detection Decision
Since the deviation is extremely large:
- The IDS classifies this as an anomaly
- It assumes that this behavior is not part of normal system activity
Step 6: Alert Generation and Response
Once the anomaly is detected, the IDS performs the following actions:
- Generates an alert to the security system
- Logs the suspicious activity
- Triggers further investigation (manual or automated)
- May initiate preventive actions (e.g., blocking IP, rate limiting)
Step 7: Real-World Interpretation
This spike could indicate:
- Brute-force attack (multiple login attempts trying different passwords)
- Credential stuffing attack
- Bot activity or automated scripts
- Malicious insider behavior
Step 8: Why This Method Works
The strength of anomaly-based IDS lies in:
- Learning normal behavior patterns
- Detecting statistical deviations
- Identifying unknown threats without predefined signatures
Even if the attack type is new, the unusual spike in activity is enough to trigger detection.
In this example, the anomaly-based IDS successfully identifies abnormal behavior by comparing real-time data against a learned baseline. The high Z-score (5) clearly indicates a strong deviation, enabling the system to flag the activity as suspicious and take immediate action.
Advantages and Disadvantages of Anomaly-Based IDS Algorithm
Anomaly-Based Intrusion Detection Systems (IDS) offer powerful capabilities for modern cybersecurity, but they also come with certain limitations. Understanding both sides is essential for effective implementation.
Advantages
- Detects Unknown Attacks: One of the most significant strengths of anomaly-based IDS is its ability to detect previously unknown or zero-day attacks. Unlike signature-based systems that rely on known attack patterns, anomaly detection focuses on deviations from normal behavior. This means even if an attack has never been seen before, the system can still flag it as suspicious if it behaves abnormally. This makes it highly effective against evolving cyber threats.
- Adaptive Learning: Anomaly-based IDS systems often incorporate machine learning and statistical models, allowing them to continuously learn and adapt. As new data is collected, the system updates its understanding of normal behavior. This adaptability ensures that the IDS remains effective even as user behavior, network patterns, or system usage evolves over time.
- Comprehensive Monitoring: These systems monitor the entire system or network behavior, rather than focusing on specific known signatures. This holistic approach allows anomaly-based IDS to detect a wide range of suspicious activities, including subtle or multi-stage attacks that might otherwise go unnoticed. It provides deeper visibility into system operations.
- Early Detection of Threats: Anomaly-based IDS can identify unusual patterns at an early stage, often before a full-scale attack occurs. For example, a sudden spike in login attempts or unusual data transfers can be detected quickly. Early detection enables faster response, reducing the potential damage caused by cyberattacks.
Disadvantages
- High False Positives : One of the biggest challenges is the high rate of false positives. Since the system flags any deviation from normal behavior, even legitimate changes (such as increased traffic during peak hours) can trigger alerts. This can overwhelm security teams and make it harder to identify real threats.
- Complex Implementation: Designing and deploying an anomaly-based IDS is technically complex. It requires expertise in machine learning, statistics, and cybersecurity. Additionally, setting appropriate thresholds and tuning the system for accuracy can be difficult and time-consuming.
- Dependency on Training Data: The effectiveness of the system heavily depends on the quality of training data. If the baseline model is built using incomplete or biased data, the IDS may fail to accurately distinguish between normal and abnormal behavior. Poor training can lead to both false positives and false negatives.
- Resource Intensive: Anomaly-based IDS systems require significant computational resources. Continuous monitoring, data processing, and real-time analysis demand high CPU, memory, and storage. This makes them more expensive to deploy and maintain compared to simpler signature-based systems.
Applications of Anomaly-Based IDS Algorithm
Anomaly-Based Intrusion Detection System (IDS) algorithms are extensively used across various industries due to their capability to detect both known and unknown threats by identifying deviations from normal behavior. These systems provide real-time monitoring and proactive security, making them essential in today’s digital landscape.
- Network Security: In network environments, anomaly-based IDS plays a vital role in monitoring and analyzing traffic patterns to identify unusual activities. It can detect sudden spikes in network traffic that may indicate Distributed Denial of Service (DDoS) attacks, as well as unauthorized access attempts and suspicious data transfers. By continuously observing network behavior, it helps organizations secure enterprise networks, protect data centers, and maintain the integrity of internet infrastructure.
- Financial Systems: In the financial sector, anomaly detection is widely used to identify fraudulent transactions and protect user accounts. By analyzing transaction patterns and user behavior, the system can detect unusual spending activities, transactions from unfamiliar geographic locations, and rapid multiple transactions within a short time frame. This enables banks and financial institutions to respond quickly to potential fraud, reducing financial losses and enhancing customer trust.
- Cloud Computing: Anomaly-based IDS is highly effective in cloud computing environments, where systems are dynamic and distributed. It monitors virtual machines, user access patterns, and API usage to detect suspicious activities. This includes identifying unauthorized access, potential data breaches, and insider threats. By providing continuous surveillance, it ensures the security and reliability of cloud services and infrastructure.
- Industrial Control Systems (ICS): In industries such as manufacturing, energy, and utilities, anomaly detection is used within Industrial Control Systems (ICS), including SCADA and IoT environments. The system monitors equipment behavior, sensor outputs, and control commands to ensure normal operations. Any abnormal deviation may signal a cyberattack or system malfunction, allowing organizations to take immediate corrective action and prevent operational disruptions or safety risks.
- Healthcare Systems: Healthcare organizations rely on anomaly-based IDS to safeguard sensitive patient data and maintain compliance with regulatory standards. The system detects unauthorized access to medical records, unusual system usage patterns, and potential data leaks. By ensuring data confidentiality and integrity, it plays a crucial role in protecting patient privacy and securing healthcare information systems.
- E-commerce Platforms: In e-commerce platforms, anomaly detection is used to monitor user behavior and prevent fraudulent activities. It can identify fake account creation, detect bot traffic, and recognize unusual purchasing patterns that may indicate fraud. This helps businesses maintain platform integrity, prevent financial losses, and build customer confidence by providing a secure online shopping experience.
Conclusion
The Anomaly-Based Intrusion Detection System (IDS) Algorithm has become a cornerstone of modern cybersecurity due to its ability to go beyond traditional, rule-based detection methods. Instead of relying on predefined attack signatures, it focuses on identifying deviations from established normal behavior. This fundamental approach enables organizations to detect not only known threats but also previously unseen attacks, including zero-day vulnerabilities that often bypass conventional security systems. One of the key strengths of anomaly-based IDS lies in its proactive nature. By continuously monitoring system and network activity, it can identify subtle irregularities at an early stage—often before they escalate into serious security incidents. Whether it is an unusual spike in login attempts, abnormal data transfers, or unexpected user behavior, the system provides early warning signals that allow security teams to respond quickly and effectively. However, despite its advantages, anomaly-based IDS is not without challenges. High false positive rates remain a significant concern, as legitimate changes in user or system behavior can sometimes be misclassified as threats. Additionally, the complexity of implementation, the need for high-quality training data, and the computational resources required for real-time analysis can pose practical limitations for organizations. To address these challenges, modern anomaly-based IDS solutions are increasingly integrating advanced technologies such as machine learning and artificial intelligence. These enhancements enable the system to improve its accuracy over time, reduce false alarms, and adapt to dynamic environments. Techniques like deep learning, behavioral analytics, and adaptive thresholding are making anomaly detection more intelligent and reliable.
In today’s rapidly evolving threat landscape, where cyberattacks are becoming more sophisticated and unpredictable, relying solely on traditional security mechanisms is no longer sufficient. Anomaly-based IDS provides a critical additional layer of defense by offering visibility into unknown and emerging threats. In conclusion, organizations that adopt and properly implement anomaly-based IDS algorithms can significantly strengthen their cybersecurity posture. By combining continuous monitoring, intelligent analysis, and adaptive learning, these systems help minimize risks, protect sensitive data, and ensure the resilience of digital infrastructures in the face of ever-growing cyber threats.
Frequently Asked Questions (FAQs)
What is the main purpose of an Anomaly-Based IDS?
The main purpose is to detect unusual patterns in system behavior that may indicate cyber threats.
How are anomaly-based IDS different from signature-based IDS?
Anomaly-based IDS detects unknown attacks by identifying deviations, while signature-based IDS detects known threats using predefined patterns.
What causes false positives in anomaly detection?
Changes in normal behavior, poor training data, or incorrect threshold settings can lead to false positives.
Which techniques are used in anomaly-based IDS?
Common techniques include statistical analysis, machine learning, clustering, and neural networks.
Is anomaly-based IDS suitable for real-time detection?
Yes, it is widely used for real-time monitoring, though it requires efficient processing and tuning.