What is Signature-Based IDS Algorithm?
A Signature-Based Intrusion Detection System (IDS) Algorithm is a cybersecurity mechanism that detects malicious activities by comparing network traffic or system behavior against a database of known attack patterns, called signatures. These signatures are predefined rules that represent known threats such as malware, viruses, worms, or specific attack techniques. In simple terms, it works like antivirus software:
If the incoming data matches a known malicious pattern, the system flags it as a threat.Signature-based IDS is widely used in network security due to its accuracy in identifying known attacks with minimal false positives.
Introduction of Signature-Based IDS Algorithm
With the rapid growth of digital systems, networks have become increasingly vulnerable to cyberattacks. Organizations require reliable systems to monitor, detect, and respond to threats in real time. This is where Intrusion Detection Systems (IDS) play a critical role. A Signature-Based IDS Algorithm is one of the earliest and most widely adopted detection approaches. It relies on a database of known attack signatures and continuously scans incoming and outgoing traffic to identify matches.
Key Characteristics:
- Detects known threats effectively
- Uses pattern matching techniques
- Requires regular updates to signature database
- Provides high accuracy with low false positives
Unlike anomaly-based IDS, which detects deviations from normal behavior, signature-based IDS focuses only on predefined attack patterns.
Detailed Signature-Based IDS Algorithm
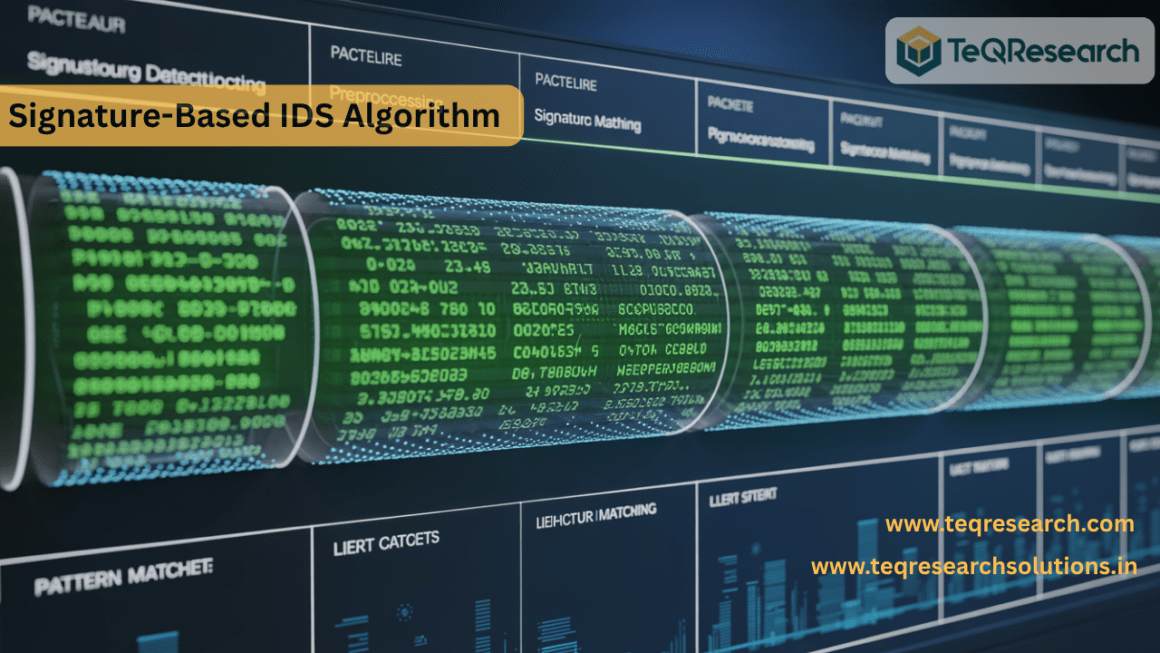
The Signature-Based IDS algorithm operates through a sequence of steps involving data collection, feature extraction, signature matching, and alert generation.
Step 1: Data Collection
The IDS captures network packets or system logs.
Let:
- P={p1,p2,p3,…,pn} be the set of incoming packets.
Each packet contains:
- Source IP (IPs)
- Destination IP (IPd)
- Payload (D)
- Protocol (Pr)
Step 2: Preprocessing
Noise removal and normalization of data.

Where:
- P′ is the cleaned dataset.
Step 3: Feature Extraction
Extract relevant attributes from packets.

Where:
- Fi = Feature vector of packet pi
Example features:
- Packet size
- Header fields
- Payload patterns
Step 4: Signature Database
Let:
- S={s1,s2,s3,…,sm}
Each signature represents:
- Known attack pattern
- Regular expression or byte sequence
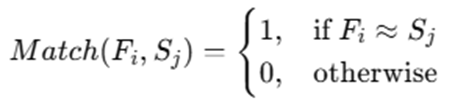
Step 5: Pattern Matching
Compare extracted features with stored signatures:
Step 6: Decision Rule
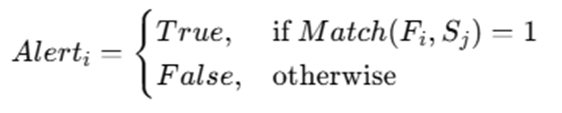
Step 7: Alert Generation
If a match is found:
- Raise alert
- Log event
- Trigger response system
Step 8: Database Update
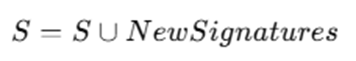
Signature database must be updated regularly to detect new threats.
The Signature-Based IDS Algorithm begins by capturing incoming network traffic or system logs in real time. Each packet of data is collected and passed into the preprocessing stage, where irrelevant or redundant information is removed, and the data is normalized for consistent analysis. This step ensures that variations in packet formats do not affect detection accuracy. Once preprocessing is complete, the system performs feature extraction. In this phase, essential attributes such as packet headers, payload content, source and destination IP addresses, and protocol types are extracted. These features form a structured representation of each packet, enabling efficient comparison with known attack patterns.
The algorithm then accesses a signature database, which contains predefined patterns representing known threats. These signatures may be stored as byte sequences, regular expressions, or rule-based definitions. The extracted features of each packet are compared against these signatures using pattern matching techniques. If a match is found between a packet’s features and any stored signature, the system identifies it as malicious. A decision rule is applied to confirm whether the match is significant enough to trigger an alert. Once confirmed, the IDS generates an alert, logs the incident, and may initiate predefined response actions such as blocking the traffic or notifying administrators.Finally, the system continuously updates its signature database to include newly discovered threats. This ensures that the IDS remains effective against evolving cyberattacks. However, it is important to note that the system can only detect threats that already have known signatures.
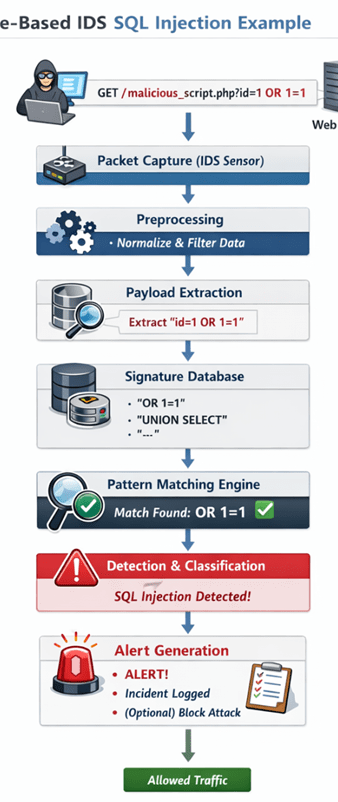
Example of How Signature-Based IDS Algorithm Works
To understand how a Signature-Based IDS Algorithm works in practice, let’s walk through a detailed real-world example involving a common web attack—SQL Injection.
Example Scenario
A user sends a request to a web server. However, instead of a normal request, the attacker injects malicious SQL code into the URL.
Captured Network Packet Payload:
GET /malicious_script.php?id=1 OR 1=1 HTTP/1.1
Host: example.com
Signature Stored in IDS Database:
“OR 1=1”
This pattern is a well-known SQL injection signature used to bypass authentication or manipulate database queries.
Step-by-Step Detection Process
Packet Capture
The IDS continuously monitors network traffic. When the attacker sends the malicious request, the IDS captures the packet in real time.
Let:

This packet contains:
- HTTP request method (GET)
- URL with parameters
- Payload containing suspicious query
Payload Extraction
The IDS extracts the payload from the packet for inspection.

From the packet:
D = “id=1 OR 1=1”
This step isolates the critical part of the request where attacks are most likely embedded.
Feature Identification
The system analyzes the payload and identifies patterns or tokens.
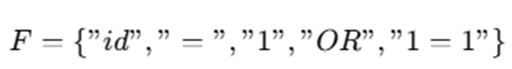
Here, the keyword “OR” combined with a condition like “1=1” is a strong indicator of SQL injection.
Signature Matching
The extracted payload is compared against known signatures in the database.
Let:

Matching function:
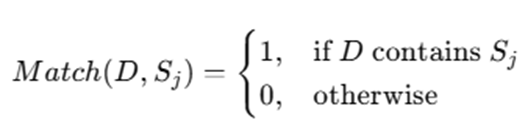
Since:
D contains “OR 1=1”
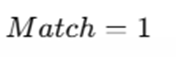
Attack Classification
Once a match is found, the IDS classifies the type of attack based on the matched signature.
Matched Signature: “OR 1=1”
Attack Type: SQL Injection
This classification helps in logging and response handling.
Alert Generation
The IDS triggers an alert to notify the system administrator or security system.
Generated Alert Example:
- Threat Type: SQL Injection
- Source IP: Attacker’s IP
- Target: Web Server
- Severity: High
Response Action (Optional)
Depending on system configuration, the IDS or integrated IPS (Intrusion Prevention System) may take action:
- Block the IP address
- Drop the packet
- Log the attack
- Notify administrator
In this example, the Signature-Based IDS begins by capturing a network packet containing an HTTP request. The system extracts the payload, focusing on parameters passed in the URL. It then analyzes the payload and identifies suspicious patterns, such as logical operators and conditions commonly used in SQL injection attacks. The extracted data is compared against a database of known attack signatures. When the pattern “OR 1=1” is detected within the payload, the IDS recognizes it as a known SQL injection signature. Based on this match, the system classifies the activity as a malicious attack and generates an alert. Depending on the system’s configuration, it may also take preventive actions such as blocking the request or logging the event for further investigation. This entire process happens in real time, allowing organizations to quickly detect and respond to known threats.
Advantages and Disadvantages of Signature-Based IDS Algorithm
Advantages of Signature-Based IDS Algorithm
- High Accuracy for Known Attacks: One of the biggest strengths of a Signature-Based IDS is its ability to detect known threats with very high precision. Since the system relies on predefined attack signatures, it can accurately identify malicious patterns without ambiguity. For example, if a signature for SQL injection like “OR 1=1” exists in the database, any packet containing that pattern will be reliably flagged. This precision makes it highly effective in environments where known threats are common.
- Low False Positives: Signature-based detection produces very few false alarms compared to other methods. Because it only triggers alerts when an exact or near-exact match is found, normal or benign traffic is rarely misclassified as malicious. This reduces the workload on security teams, as they do not need to investigate large numbers of false alerts, improving operational efficiency.
- Efficient Performance: The algorithm is generally fast and computationally efficient. Pattern matching techniques such as string matching or rule-based comparison are less resource-intensive than behavior analysis used in anomaly-based systems. This makes signature-based IDS suitable for real-time detection, even in high-speed networks with large volumes of traffic.
- Easy to Understand and Implement: Signature-Based IDS is based on a simple and transparent concept—matching patterns. Security professionals can easily understand how detections are made because each alert corresponds to a specific signature. This simplicity also makes it easier to configure, maintain, and troubleshoot compared to more complex machine learning-based systems.
- Widely Adopted in Industry: This approach is widely used in commercial and open-source security tools, including firewalls, antivirus software, and network IDS solutions. Its proven reliability and ease of deployment have made it a standard component in cybersecurity infrastructures across organizations of all sizes.
Disadvantages of Signature-Based IDS Algorithm
- Cannot Detect Unknown Attacks (Zero-Day Threats): The biggest limitation is that it can only detect known attacks. If a new or modified attack does not match any existing signature, the IDS will fail to detect it. These are known as zero-day attacks, and they pose a significant risk because signature-based systems have no prior knowledge of them.
- Requires Frequent Updates: The effectiveness of the system depends heavily on the signature database being up to date. New threats emerge constantly, and without regular updates, the IDS becomes outdated and less effective. Maintaining and updating signatures can be time-consuming and requires continuous monitoring of emerging threats.
- Limited Adaptability: Signature-Based IDS lacks the ability to learn or adapt automatically. Unlike modern AI-based systems, it does not analyze patterns or evolve based on new data. It strictly depends on manually created signatures, making it less flexible in dynamic threat environments.
- Large Database Overhead: As the number of known threats increases, the signature database grows larger. This leads to:
- Increased memory usage
- Slower matching processes
- Higher computational overhead
In large-scale systems, managing and searching through a massive signature database can impact performance.
- Vulnerable to Evasion Techniques: Attackers can use various techniques to bypass signature detection, such as:
- Obfuscating payloads
- Encoding malicious content
- Splitting attack patterns across multiple packets
For example, instead of sending “OR 1=1” directly, an attacker might modify it slightly to avoid matching the exact signature. Since the IDS relies on exact or predefined patterns, such variations may go undetected.
Applications of Signature-Based IDS Algorithm
Signature-Based IDS algorithms are widely used across different domains of cybersecurity because of their ability to accurately detect known threats. Below is a detailed explanation of their major applications:
- Network Security Monitoring: Signature-Based IDS plays a crucial role in monitoring network traffic within organizations. It continuously inspects incoming and outgoing data packets to detect known attack patterns such as port scans, denial-of-service (DoS) attacks, and malware communication. In enterprise environments, IDS sensors are placed at key points in the network (e.g., gateways, routers, or switches). These systems analyze traffic in real time and generate alerts whenever a signature match is found. This helps organizations quickly identify and respond to threats before they cause damage.
- Antivirus Systems: One of the most common applications of signature-based detection is in antivirus software. Antivirus programs maintain large databases of known malware signatures, including viruses, worms, trojans, and ransomware. When a file is scanned, the antivirus compares its contents against the signature database. If a match is found, the file is flagged as malicious and appropriate action is taken, such as quarantine or deletion. This approach is highly effective for detecting known malware variants and is still a core component of modern endpoint security solutions.
- Firewall Integration: Signature-Based IDS is often integrated with firewalls to enhance network perimeter security. While traditional firewalls filter traffic based on rules like IP addresses and ports, IDS adds an additional layer of intelligence by analyzing packet content. For example, even if traffic is allowed through a firewall, the IDS can detect hidden malicious patterns within the payload. This combination creates a more robust defense system, often referred to as Intrusion Detection and Prevention Systems (IDPS).
- Data Centers: In data centers, where large volumes of sensitive data are processed and stored, Signature-Based IDS is used to protect servers and infrastructure from known threats.
It monitors:
- Server communications
- Database queries
- Internal traffic between systems
By detecting known attack signatures, the IDS helps prevent unauthorized access, data breaches, and service disruptions. This is especially important for cloud service providers and large-scale enterprise environments.
- Web Application Security: Signature-Based IDS is widely used to secure web applications against common attacks such as:
- SQL Injection
- Cross-Site Scripting (XSS)
- Command Injection
It inspects HTTP requests and responses to identify malicious input patterns. For instance, detecting strings like “OR 1=1” or <script> tags helps prevent attackers from exploiting web application vulnerabilities. This functionality is often implemented through Web Application Firewalls (WAFs), which rely heavily on signature-based detection techniques.
- Government & Military Systems: Government and military organizations use Signature-Based IDS to safeguard critical infrastructure and sensitive information systems. These environments require highly reliable and accurate detection mechanisms to defend against known cyber threats.
Signature-based systems are used to:
- Monitor classified networks
- Detect known cyberattack techniques
- Ensure compliance with security standards
Due to their low false positive rate and proven effectiveness, they are a trusted component in high-security environments.
Conclusion
The Signature-Based IDS Algorithm continues to play a vital role in modern cybersecurity due to its proven reliability, simplicity, and efficiency. By using a database of predefined attack signatures, it enables systems to quickly identify and respond to known threats with a high degree of accuracy. This makes it one of the most trusted and widely implemented detection techniques across networks, servers, and applications. One of the key strengths of this approach is its precision in identifying known attack patterns. Since the detection process is based on exact or rule-based matching, organizations benefit from low false positive rates, allowing security teams to focus on genuine threats rather than wasting time on unnecessary alerts. Additionally, the algorithm’s lightweight and efficient nature makes it suitable for real-time monitoring, even in high-traffic environments.
However, despite these advantages, the Signature-Based IDS Algorithm has inherent limitations. Its biggest drawback is its inability to detect unknown or zero-day attacks. Because it relies entirely on existing signatures, any new or modified attack that does not match the stored patterns can bypass detection. This limitation highlights the need for continuous updates to the signature database, which can be resource-intensive and requires ongoing attention from security professionals. To address these challenges, modern cybersecurity strategies often combine signature-based detection with anomaly-based or behavior-based systems. While signature-based IDS handles known threats efficiently, anomaly-based systems analyze unusual patterns and behaviors to detect previously unseen attacks. This hybrid approach creates a more comprehensive and adaptive security framework, capable of defending against both known and emerging threats.
As cyber threats become increasingly sophisticated, the importance of maintaining an up-to-date signature database cannot be overstated. Organizations must continuously monitor new vulnerabilities, update their detection rules, and integrate advanced technologies such as machine learning and threat intelligence platforms. In conclusion, the Signature-Based IDS Algorithm remains a cornerstone of network security, offering dependable protection against known threats. When combined with modern detection techniques and proactive security practices, it forms a strong foundation for building resilient and future-ready cybersecurity systems.
Frequently Asked Questions (FAQs)
What is the main purpose of a Signature-Based IDS?
The main purpose is to detect known cyber threats by matching network activity against predefined attack signatures.
How is Signature-Based IDS different from Anomaly-Based IDS?
Signature-based IDS detects known threats, while anomaly-based IDS identifies unusual behavior that may indicate unknown threats.
Can Signature-Based IDS detect zero-day attacks?
No, it cannot detect zero-day attacks because they do not have predefined signatures.
Why is updating the signature database important?
Updating ensures the system can detect newly discovered threats and vulnerabilities.
Where is Signature-Based IDS commonly used?
It is used in firewalls, antivirus software, enterprise networks, and data centers for threat detection.