What is Secure Hash Algorithm (SHA)?
The National Institute of Standards and Technology (NIST) publishes the Secure Hash Algorithm (SHA), a family of cryptographic hash functions created by the National Security Agency (NSA). In a variety of cryptographic applications, these algorithms are employed to guarantee data security, authenticity, and integrity. Every SHA algorithm takes an input message and creates a fixed-length hash (digest) that is different for every single input. Because even little input changes produce radically different hashes, SHA algorithms are essential to digital security. Types of Secure Hash Algorithms are:
- SHA-1 (Secure Hash Algorithm 1) : Created by the NSA in 1993 and updated in 1995. Generates a hash value of 160 bits. NIST formally deprecated it, citing collision attacks as the reason for its perceived weakness.
- SHA-2 (Secure Hash Algorithm 2): Launched in 2001 as SHA-1’s replacement. Consists of the following versions: SHA-512, SHA-512/224, SHA-256, SHA-384, SHA-512, and SHA-512/256. Has more robust cryptographic qualities and is frequently utilized in blockchain, SSL certificates, and digital signatures.
- SHA-3 (Secure Hash Algorithm 3): 2015 saw the standardization of the Keccak algorithm. In contrast to SHA-1 and SHA-2, it employs an entirely different structure (sponge construction). Is regarded as the most secure member of the SHA family and provides greater resistance to cryptographic assaults.
Introduction to Secure Hash Algorithm (SHA-1, SHA-2, SHA-3)
A family of cryptographic hash functions known as Secure Hash Algorithms (SHA) was created to guarantee data confidentiality, integrity, and authenticity in online applications. An input message is transformed by these methods into a fixed-length hash value that uniquely identifies the data. The avalanche effect is a feature that causes the hash to change significantly even with a slight change in the input.
Development and Evolution
The National Institute of Standards and Technology (NIST) disclosed the SHA family, which was created by the National Security Agency (NSA). New iterations of SHA were released over time as processing power grew and security flaws were found:
- SHA-1 (1993, Revised 1995)
- The first cryptographic hash function to be extensively used.
- Generates a hash value of 160 bits.
- Officially deprecated by NIST in 2011, this system is susceptible to collision assaults.
- SHA-2 (2001)
- A more secure and enhanced version of SHA-1.
- Consists of six variations: SHA-512, SHA-512/224, SHA-256, SHA-384, SHA-512, and SHA-512/4.
- Widely utilized in SSL/TLS security, blockchain, and digital signatures.
- SHA-3 (2015)
- Distinct from SHA-1 and SHA-2, and based on the Keccak algorithm.
- Sponge construction improves protection against intrusions.
- Offers SHA-2 a more adaptable and safe substitute.
Why Was SHA-3 Introduced?
Although SHA-2 is still safe, SHA-3 was created in response to the growing threat of quantum computing and sophisticated cryptanalysis. In contrast to SHA-1 and SHA-2, SHA-3 employs the Keccak sponge construction instead of the Merkle-Damgård structure, which makes it impervious to known flaws.
Secure Hash Algorithm (SHA-1, SHA-2, SHA-3) – Detailed Explanation
Cryptographic hash functions use a number of intricate mathematical operations to convert an input message into a fixed-length hash (digest). Every SHA algorithm adheres to a different procedure to guarantee data security, uniqueness, and integrity. A detailed explanation of SHA-1, SHA-2, and SHA-3 can be found below.
SHA-1 (Secure Hash Algorithm 1) – Step-by-Step Process
1. Message Padding
- A 512-bit alignment is achieved by padding the input message.
- Until the length is 64 bits less than a multiple of 512, a 1 bit is attached, followed by 0s.
- The original message length is stored in the final 64 bits.
2. Message Block Processing
- The padded message is divided into 512-bit blocks.
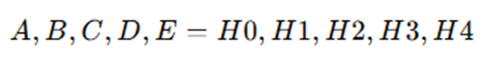
- Each block is processed using a 160-bit hash state initialized with fixed values:

3. Message Expansion & Hash Computation
- Each 512-bit block is expanded into 80 words (W[0] to W[79]) using:
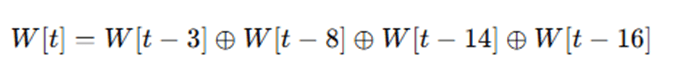
- The compression function updates the hash state using bitwise operations:
For each round (t = 0 to 79):
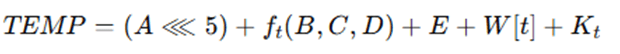
where K_t is a constant and f_t(B,C,D) is a nonlinear function.
- After all rounds, the hash values are updated and concatenated to produce the 160-bit hash.
Weakness & Deprecation
- SHA-1 is vulnerable to collision attacks (two different messages producing the same hash).
- NIST deprecated SHA-1 in 2011, recommending SHA-2 and SHA-3.
SHA-2 (SHA-224, SHA-256, SHA-384, SHA-512) – Step-by-Step Process
SHA-2 improves SHA-1 by using larger hash values, stronger bitwise operations, and different message expansion techniques.
1. Message Padding
- Similar to SHA-1, the message is padded so its length is multiple of 512 bits (SHA-256) or 1024 bits (SHA-512).
2. Initialization of Hash Values
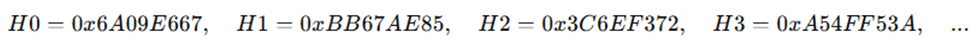
- Uses a larger initial hash state than SHA-1. For SHA-256:
3. Message Expansion & Hash Computation
- The message is divided into 512-bit (SHA-256) or 1024-bit (SHA-512) blocks.
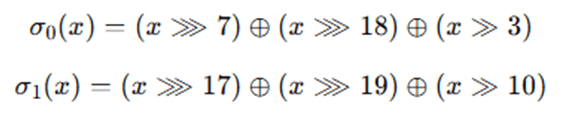
- Each block is expanded using a modified formula:
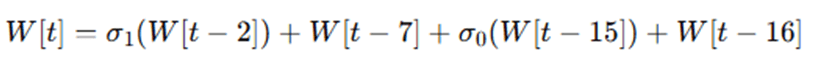
Where
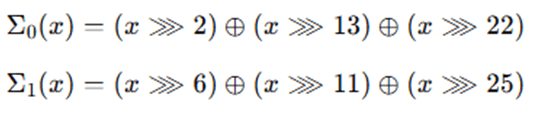
- The compression function updates the state using:
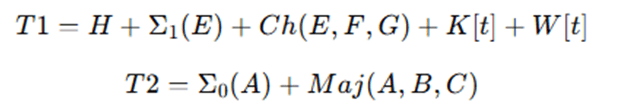
Where
- After 64 rounds (SHA-256) or 80 rounds (SHA-512), the final digest is obtained.
Security Improvements Over SHA-1
- Stronger resistance against collision attacks.
- Larger hash values (256-bit, 384-bit, 512-bit).
SHA-3 (Keccak Algorithm) – Step-by-Step Process
Unlike SHA-1 and SHA-2, SHA-3 is based on the Keccak sponge construction, which absorbs and squeezes data for security.
1. Message Padding
- Message is padded using a unique padding rule that ensures security against length-extension attacks.
2. Sponge Construction
- The input is processed in a sponge function with:
- Absorbing phase: The input message is XORed into a state matrix and permuted.
- Squeezing phase: The final hash is extracted by iterating the Keccak function.
3. Keccak Permutation Function
- Uses bitwise XOR, rotation, and substitution to update a 5×5 matrix of 64-bit lanes.
- Each round consists of:
- Theta (θ) transformation
- Rho (ρ) transformation
- Pi (π) transformation
- Chi (χ) transformation
- Iota (ι) transformation
Security Benefits of SHA-3
- More resistant to side-channel attacks.
- No length-extension vulnerabilities.
- More efficient on hardware implementations.
Comparison of SHA-1, SHA-2, and SHA-3
| Feature | SHA-1 | SHA-2 | SHA-3 |
| Hash Size | 160-bit | 224, 256, 384, 512-bit | 224, 256, 384, 512-bit |
| Security | Weak (Collision found) | Strong | Strongest |
| Structure | Merkle-Damgård | Merkle-Damgård | Sponge Function |
| Speed | Fast | Moderate | Slower in software, fast in hardware |
| Use Case | Deprecated | Widely Used | Future-proof |
All three members of the Secure Hash Algorithm (SHA) family—SHA-1, SHA-2, and SHA-3—are intended to generate a fixed-length hash result from a variable-length input, although they operate via distinct internal methods. SHA-3 employs a totally new sponge construction, although SHA-1 and SHA-2 have comparable structures based on the Merkle–Damgård construction. The broad, step-by-step description that follows focuses on the inner workings of SHA-1 and SHA-2 before going on to discuss the special procedure of SHA-3.
Preprocessing is the first step in the process, which involves padding the input message to make sure its length is greater than a predetermined block size (512 bits for SHA-1 and SHA-2 variations like SHA-256). Adding a single “1” bit, enough “0” bits, and then a 64-bit representation of the original message length is the standard padding procedure. This avoids ambiguity and guarantees message alignment. Next, the padded message is divided into blocks of equal size (e.g., 512-bit blocks for SHA-1 and SHA-256). Each block is then processed sequentially through the algorithm’s compression function. Before processing, a set of initial hash values is established. For SHA-1, five 32-bit variables are used, while SHA-256 uses eight 32-bit variables. These values are derived from the square roots of the first few prime numbers.
A message schedule of 80 words for SHA-1 or 64 words for SHA-256 is created by expanding each 512-bit block into 16 words, each of which is made up of 32 bits. Certain logical operations, including shifts, XOR operations, and bitwise rotations, are used in this extension. The internal state (the hash values) is then changed using modular addition, bitwise logical operations, and specified constants in a sequence of rounds that use the enlarged message schedule (80 rounds for SHA-1 and 64 rounds for SHA-256). In order to guarantee high diffusion and complexity, the message data is mixed into the hash state in each round. After all blocks are processed, the final hash value is obtained by concatenating the updated values of the hash state. For instance, SHA-256 outputs a 256-bit (32-byte) hash value by combining eight 32-bit words.
In contrast, SHA-3 uses a sponge architecture to function. After being padded using a reversible padding algorithm, the input message is divided into capacity and bitrate sections and absorbed into a 1600-bit state matrix. The Keccak-f permutation, which consists of five internal steps (Theta, Rho, Pi, Chi, and Iota) to guarantee diffusion and non-linearity, is used to repeatedly alter the message once it has been XORed into the state. The state is compressed to create the output hash of the required length (256 bits for SHA3-256, for example) once all of the input has been absorbed. SHA-3 has no known structural flaws and is immune to length-extension assaults, in contrast to SHA-2. In SHA-3 presents a completely different structure targeted at future-proof cryptographic strength, whereas SHA-1 and SHA-2 use iterative, block-based processing with similar logic. The fundamental objective of all SHA algorithms, notwithstanding structural variations, is to safely convert input data into a fixed-size, irreversible hash that accurately captures the original message.
Advantages and Disadvantages of SHA Algorithms
Secure Hash Algorithms (SHA), including SHA-1, SHA-2, and SHA-3, are cryptographic hash functions used to ensure data integrity, verify authenticity, and secure digital communication. While these algorithms provide essential benefits in cryptographic systems, they also come with certain limitations, especially as newer technologies and threats emerge.
Advantages of SHA
- Data Integrity: SHA ensures that data has not been altered during transmission. Even a small change in the input results in a completely different hash, making tampering easily detectable.
- One-Way Function: SHA algorithms are irreversible; it is computationally infeasible to retrieve the original input from the hash value, which is critical for password storage and data security.
- Collision Resistance: SHA-2 and SHA-3 are designed to be collision-resistant, meaning it’s nearly impossible for two different inputs to produce the same hash, thus ensuring uniqueness.
- Broad Application Support: SHA is widely used in digital signatures, SSL/TLS, blockchain, email security, and file integrity verification, making it a backbone of modern digital security.
- Scalable Security Levels: SHA-2 provides different versions (e.g., SHA-224, SHA-256, SHA-384, SHA-512) to balance security and performance needs. SHA-3 allows variable-length outputs and provides enhanced flexibility.
- Hardware and Software Efficiency: SHA algorithms, especially SHA-2 and SHA-3, are efficient in both hardware and software implementations, enabling use in embedded systems, IoT devices, and mobile platforms.
Disadvantages of SHA
- SHA-1 Security Weakness : SHA-1 is no longer secure. It has been successfully broken with collision attacks, and its use is deprecated by major organizations like NIST.
- Computational Cost : SHA-2 (e.g., SHA-512) requires more processing power and time than older algorithms like MD5 or SHA-1, which may affect performance in low-power environments.
- Quantum Vulnerability: SHA-2 is theoretically vulnerable to quantum computing attacks via Grover’s algorithm, which could halve its effective security strength in the future.
- Slow Adoption of SHA-3: Despite its robust design, SHA-3 has not yet seen widespread adoption. Most systems still rely on SHA-2, potentially delaying advancements in cryptographic standards.
- Length Extension Attacks on SHA-2: While SHA-2 is secure, it is vulnerable to length extension attacks, which can be exploited in certain scenarios unless properly mitigated. SHA-3’s sponge construction solves this issue.
Summary Table: SHA Algorithm Pros and Cons
| Feature | SHA-1 | SHA-2 | SHA-3 |
| Security Level | Weak (Broken) | Strong | Very Strong (Post-Quantum) |
| Collision Resistance | Low | High | Very High |
| Efficiency | Fast | Moderate | High (in hardware) |
| Structure | Merkle-Damgård | Merkle-Damgård | Sponge (Keccak) |
| Vulnerable to Attacks | Yes (Collisions) | Length Extension | No known practical weaknesses |
| Widespread Use | Deprecated | Widely Adopted | Growing Adoption |
While SHA algorithms have greatly enhanced data security and integrity in digital systems, they must evolve alongside emerging threats. SHA-2 currently balances performance and security well, but SHA-3 is positioned as a future-proof solution designed to withstand even quantum threats. Moving away from outdated algorithms like SHA-1 is critical to maintaining robust cybersecurity.
Applications of Secure Hash Algorithm
SHA-1, SHA-2, and SHA-3 secure hash algorithms are widely used in data integrity verification, cryptography, and cybersecurity. The main uses for each SHA version are listed below.
- Digital Signatures and Certificates: To guarantee document authenticity and guard against manipulation, SHA-2 and SHA-3 are widely utilized in digital signatures and Public Key Infrastructure (PKI). Web browser SSL/TLS certificates encrypt HTTPS communications by using SHA-256. However, because of security flaws, SHA-1 is no longer used in SSL/TLS certificates.
- Cryptographic Hashing in Password Storage: While SHA-1 is no longer secure, SHA-256 and SHA-512 are still used in salting and hashing passwords to thwart brute-force attacks. Websites store passwords as SHA hash values instead of plain text to improve security. SHA functions are used internally by modern password hashing algorithms like Argon2 and Bcrypt.
- Blockchain and Cryptocurrencies: The fundamental hashing function of Bitcoin and numerous other cryptocurrencies is SHA-256, which is also utilized in mining algorithms, transaction verification, and wallet address generation. Because of its improved security properties, SHA-3 is becoming more and more popular in blockchain technology.
- Data Integrity Verification: By comparing hash values before and after transmission, SHA algorithms make sure that files and software updates haven’t been altered. Checksum verification for file integrity in operating systems and software downloads uses SHA-256 and SHA-3. SHA-3 is advised by ISO standards for next-generation data integrity verification.
- Secure Communication (SSL/TLS, VPNs, and Email Security): SHA-256 is used by VPN and TLS (Transport Layer Security) encryption technologies for safe data transfer. SHA hashing is used by S/MIME email encryption and PGP (Pretty Good Privacy) to guarantee the validity of messages. SHA-3 is being investigated for encryption systems that are resistant to quantum errors.
- Digital Forensics and Legal Evidence: Legal authorities employ SHA-256 or SHA-512 to validate papers and files in court cases. Hashing is used in forensic investigations to assure the integrity of digital evidence.
- Internet of Things (IoT) and Embedded Systems: SHA-3 is favored in hardware implementations because of its effectiveness and security. Secure hash functions are used in IoT devices to authenticate firmware updates and stop malware attacks.
Comparison of SHA Applications,
| Application | SHA-1 | SHA-2 | SHA-3 |
| SSL/TLS & Digital Signatures | Deprecated | Widely used (SHA-256) | Future adoption |
| Password Hashing | Weak | Used (SHA-256, SHA-512) | Secure |
| Blockchain | Not used | Bitcoin (SHA-256) | Possible future use |
| Data Integrity | Weak | Strong | Strongest |
| Forensics | Not recommended | Used in courts | Advanced security |
| IoT Security | Not suitable | Used | Best for embedded systems |
In SHA algorithms are essential to data integrity, digital security, and contemporary cryptography.
- SHA-1 is insecure and out of date.
- For the majority of security applications, SHA-2 continues to be the industry standard.
- SHA-3 is made to meet the demands of cryptography in the future, particularly in the area of quantum-resistant security.
Conclusion
In contemporary cryptography, the Secure Hash Algorithm (SHA) family is essential for guaranteeing data confidentiality, integrity, and authenticity in a variety of applications. Once widely used, SHA-1 is no longer appropriate for secure applications because of its susceptibility to collision attacks. Because of its strong security characteristics, SHA-2—in particular, SHA-256 and SHA-512—has emerged as the industry standard for digital signatures, SSL/TLS encryption, blockchain technology, and password hashing. With its distinct sponge structure, SHA-3, on the other hand, offers even more defense against cryptographic assaults and is built for future-proof security, particularly against new threats from quantum computing. SHA-3 is becoming more popular for high-security applications, even though SHA-2 is still the most often used algorithm in modern systems. Switching to more secure hash algorithms like SHA-3 will be crucial to preserving data integrity and cryptographic resilience in the digital world as cybersecurity threats continue to change.
Frequently Asked Questions (FAQs)
1. Why is SHA-1 considered insecure?
Answer: Because of its susceptibility to collision attacks, in which two distinct inputs generate the same hash, SHA-1 is regarded as unsafe. In 2017, researchers proved that SHA-1 is no longer secure for cryptographic purposes by successfully demonstrating a viable collision attack, often known as the SHAttered attack.
2. What is the main difference between SHA-2 and SHA-3?
Answer: SHA-3 is more resilient to length-extension attacks because it employs the Keccak sponge construction, whereas SHA-2 is based on the Merkle-Damgård structure. Additionally, SHA-3 is better equipped to handle upcoming cryptographic difficulties, such as threats from quantum computing.
3. Which SHA version is best for password hashing?
Answer: Although they are occasionally employed for password hashing, SHA-256 and SHA-512 are not the best options when used alone. By incorporating SHA algorithms and adding salt and many rounds to slow down brute-force assaults, secure password hashing functions like bcrypt, PBKDF2, and Argon2 improve security.
4. How is SHA-256 used in blockchain technology?
Answer: The fundamental hashing algorithm used by Bitcoin and other cryptocurrencies is SHA-256. It creates wallet addresses, guarantees proof-of-work mining, and protects transaction data. SHA-256’s irreversible nature contributes to the security and integrity of blockchain networks.
5. Will SHA-3 replace SHA-2 in the future?
Answer: Because of its extensive use, SHA-2 is still the standard even if SHA-3 provides more security. Although post-quantum cryptography and high-security applications are expected to utilize SHA-3, most systems will still employ SHA-2 unless new weaknesses are found.