What is Message Digest Algorithm (MD5)
Ronald Rivest created the cryptographic hash algorithm known as the Message Digest Algorithm 5 (MD5) in 1991. It is frequently used to convert any length of input message into a 128-bit hash value. A fixed-size digest that accurately captures the original data is the output. Key Features of MD5 are:
- Produces a hash value that is 128 bits (16 bytes).
- Any size input can be transformed into an output with a set length.
- Utilizes compression functions, bitwise operations, and modular additions.
- Rather of encrypting data, this design verifies data integrity.
By producing a hash that functions as a fingerprint of the original data, MD5 was developed to guarantee data integrity. It is frequently used in digital signatures, file verification, and checksums to identify data changes. However, because MD5 is susceptible to collision attacks, which allow two distinct inputs to produce the same hash, it is no longer regarded as secure. Stronger hashing algorithms like SHA-256 are currently used in modern cryptography applications.
Introduction of Message Digest Algorithm (MD5)
A hash function is a mathematical operation that transforms arbitrary-length input data into a fixed-length output known as a digest or hash value. In cryptography, hash functions are frequently employed to guarantee security, authentication, and data integrity.
Development of MD5,
Ronald Rivest created the Message Digest Algorithm 5 (MD5) in 1991 to improve upon the MD4 algorithm. For any input message, it was intended to generate a 128-bit hash value. MD5 gained popularity for digital signatures, password hashing, and checksums.
Characteristics of MD5,
- Fixed Output Size: Produces a 128-bit hash (32 hexadecimal characters).
- Deterministic: The hash produced by the same input is always the same.
- Fast Computation: Made to process data quickly.
- Irreversible: Since the hashing process is one-way, the hash cannot be used to determine the original input.
- Used for Integrity Checking: Frequently used for data validation and file verification.
Importance of MD5 in Early Cryptographic Applications,
At first, MD5 was thought to be a safe and effective method for use in cryptography. Digital signatures, message authentication, and password hashing were among its applications. However, it was replaced by more robust hash algorithms like SHA-256 once security flaws were found. File checksums and fingerprinting are two examples of non-security-critical applications that nonetheless employ MD5.
Detailed Explanation of Message Digest Algorithm (MD5)
MD5 generates a 128-bit hash value after processing an input message in 512-bit blocks. It goes through a number of stages, such as output production, message processing, and padding. A detailed explanation of the MD5 algorithm may be found below.
Step 1: Padding the Message
To guarantee that the input message is 448 bits modulo 512—that is, 64 bits less than a multiple of 512—it is padded. The final message length is guaranteed to be a multiple of 512 bits because to padding.
Padding Rules:
- Append a single ‘1’ bit to the message.
- Followed by ‘0’ bits until the length is 64 bits short of a multiple of 512.
- Example:
- Original message: “Hello” (40 bits)
- Padded message: “Hello1000…000” (512-bit block)
Step 2: Appending Length
After padding, a 64-bit representation of the original message length (before padding) is added to the end of the message.
- If the original message is L bits long, append L (mod 2³²) in 64-bit format.
- The final message size is now a multiple of 512 bits.
Step 3: Initializing MD Buffer
MD5 uses four 32-bit registers initialized with the following fixed values:

These values serve as the initial state of the hash computation.
Step 4: Processing Message in 512-bit Blocks
Each 512-bit block is divided into sixteen 32-bit words and processed through four rounds of operations (each with 16 steps).
Processing Steps:
Each round consists of a nonlinear function (F, G, H, I), modular addition, and bitwise rotation.
Round 1: Nonlinear Function F
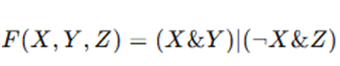
- Mixes input bits based on logical operations.
Round 2: Nonlinear Function G
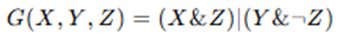
- Further shuffles bits.
Round 3: Nonlinear Function H
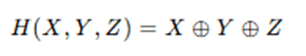
- XOR operation for diffusion.
Round 4: Nonlinear Function I
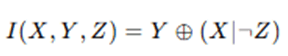
- Final transformation for randomness.
Each step updates the four registers A,B,C,D as follows:
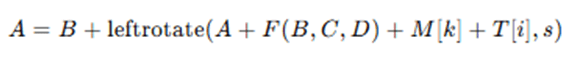
Where:
- M[k] is a 32-bit sub-block of the message.
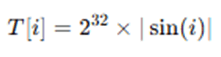
- T[i] is a constant derived from the sine function:
- s is the bitwise left rotation amount.
Step 5: Output Generation
After all 512-bit blocks are processed, the final values of registers A, B, C, D are concatenated to form the 128-bit hash value.
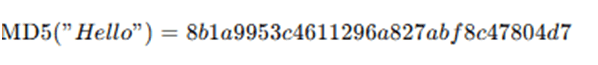
For example, the MD5 hash of “Hello” is:
Summary of MD5 Algorithm Steps:
- Padding: Extend message to make it a multiple of 512 bits.
- Appending Length: Append original message length (64 bits).
- Initialization: Set four 32-bit buffers A,B,C,DA, B, C, DA,B,C,D.
- Processing Blocks: Perform four rounds (64 operations) per block.
- Final Hash Computation: Concatenate A, B, C, D to form a 128-bit hash.
MD5 is a quick and easy hashing method; however it is no longer secure because of flaws like collision attacks. It is nonetheless often utilized in non-cryptographic applications and file integrity checks in spite of this.
The MD5 (Message Digest 5) algorithm is a cryptographic hash function that processes an input message and produces a fixed 128-bit hash value. The process begins with padding the original message. The purpose of padding is to make the length of the message congruent to 448 modulo 512. To achieve this, a single bit ‘1’ is added to the message, followed by enough ‘0’ bits to make the length 64 bits short of a multiple of 512. Then, a 64-bit representation of the original message length (before padding) is appended to the end. This ensures that the total length of the message becomes a multiple of 512 bits, as required by the algorithm.
Once the message is properly padded, the next step is to initialize four 32-bit variables, labeled A, B, C, and D, which are used as buffers to hold intermediate and final results. These are initialized to fixed hexadecimal values: A = 0x67452301, B = 0xEFCDAB89, C = 0x98BADCFE, and D = 0x10325476. The padded message is then divided into 512-bit blocks, and each block is further divided into sixteen 32-bit words. MD5 processes each block through four distinct rounds, with each round consisting of 16 operations, making a total of 64 steps per block.
Each round uses a different nonlinear function: F, G, H, and I. These functions perform bitwise logical operations on the input buffers (A, B, C, D). In each step, one of these functions is applied along with modular addition, a constant derived from the sine function (T[i]), a word from the message block, and a left circular bitwise rotation by a predefined number of bits (s). The result of each operation updates one of the four buffers. The general operation in each step can be represented as:A = B + LeftRotate((A + F(B, C, D) + M[k] + T[i]), s) ,where M[k] is one of the 32-bit words from the current block, T[i] is the sine-based constant, and s is the number of bits to rotate.
After all blocks are processed through the four rounds, the resulting values in A, B, C, and D are concatenated to produce the final 128-bit hash value. This hash value is typically represented as a 32-character hexadecimal number. The final output is the MD5 digest, which serves as a fingerprint of the input data. Even a small change in the input message results in a significantly different hash, which is a key property of cryptographic hash functions. However, due to known vulnerabilities such as collision attacks, MD5 is now considered insecure for cryptographic use, though it still remains widely used in areas like file integrity checks and basic data validation.
Advantages and Disadvantages of MD5
Advantages:
- Fast Computation: MD5 is known for its speed and efficiency, making it suitable for applications requiring quick hash calculations, such as file checksums.
- Fixed-Length Output: It produces a consistent 128-bit (16-byte) hash value regardless of the size of the input data, making it easy to store and compare.
- Deterministic Output: The same input will always generate the same hash, ensuring reliability in verification processes.
- Widely supported and implemented: MD5 is available in almost all programming languages and platforms, making it easy to integrate into existing systems.
- Useful for Integrity Verification: It is still widely used for file integrity checking, ensuring that files have not been altered during transmission or storage.
Disadvantages:
- Collision Vulnerability: MD5 is susceptible to collision attacks, where two different inputs can produce the same hash. This undermines its use in secure applications like digital signatures.
- Not Suitable for Cryptographic Security: Due to its weaknesses, MD5 is not recommended for cryptographic applications such as password hashing, encryption, or secure communication.
- Susceptible to Preimage Attacks: Given an MD5 hash, attackers can sometimes retrieve the original input using rainbow tables or brute-force methods.
- Easily Exploitable with Modern Hardware: With powerful GPUs and cloud computing, attackers can crack MD5 hashes quickly, especially for short or weak inputs.
- Lacks Forward Secrecy and Modern Cryptographic Standards: MD5 does not comply with current cryptographic best practices and is deprecated by organizations like NIST for security-sensitive tasks.
Although MD5 is still quick and popular for confirming file integrity, collision and preimage issues make it unsafe for use in cryptography. Stronger hash algorithms, such as SHA-256 or bcrypt, should be used by modern programs for security-critical operations.
Applications of MD5 Algorithm
MD5 is still often used in non-cryptographic applications where efficiency and speed are more crucial than security, despite its security flaws. Here are a few significant uses for the MD5 algorithm:
- File Integrity Verification (Checksums): MD5 is frequently used to create file checksums and assists users in confirming that a transferred or downloaded file is undamaged. Example: Software vendors provide MD5 checksums so users can confirm file integrity after downloading.
- Data Storage and Fingerprinting: Database indexing and document management systems frequently use it to generate unique identifiers by hashing big datasets. Example: File-sharing services use MD5 hashes to identify duplicate files.
- Digital Forensics and Evidence Integrity: MD5 hashes of electronic evidence are produced by law enforcement organizations to demonstrate data integrity in court; they are also used in forensic investigations to guarantee that digital evidence is preserved.
- Non-Secure Password Hashing (Legacy Systems): MD5 was once used to hash passwords in databases, however it is now regarded as insecure since it is susceptible to rainbow table and brute-force assaults. Example: Older Linux systems and web applications used MD5 for storing user passwords.
- Unique Identifier Generation: Applied to content management systems, database records, and software licenses. Example: A URL shortener service can generate a unique MD5 hash for each long URL.
- Network Security and Packet Fingerprinting: To identify changes in network packets, network security technologies use MD5. Example: Firewalls and intrusion detection systems (IDS) use MD5 hashes to detect altered or malicious packets.
- Cryptographic Applications (Historical Use): Previously utilized in SSL certificates and digital signatures, but no longer advised because of security vulnerabilities. Example: Older SSL/TLS certificates used MD5 before transitioning to SHA-256.
MD5 is still often used for file integrity checks, forensic analysis, and non-security-critical applications even though it is no longer secure for encryption or authentication. For security-sensitive jobs, modern cryptographic systems use SHA-256, bcrypt, or Argon2.
Conclusion
Once a popular cryptographic hash function, the Message Digest Algorithm 5 (MD5) was renowned for producing fixed-length 128-bit hashes quickly and effectively. Checksums, password hashing, and digital signatures all heavily relied on MD5, which was first created to guarantee data integrity and authentication. But as cryptanalysis has advanced, MD5 has been shown to be susceptible to collision attacks, in which multiple inputs might generate the same hash, rendering it inappropriate for secure applications. For non-security-critical applications like file integrity verification, digital forensics, and unique identifier generation, MD5 is nevertheless often utilized despite its flaws. Stronger algorithms like SHA-256, bcrypt, or Argon2 are advised for contemporary cryptographic requirements in order to guarantee increased security. In many non-cryptographic sectors where data integrity, not security, is the major issue, MD5 is still useful even if it has been mostly supplanted in security-sensitive applications.
Frequently Asked Questions (FAQs)
Q1. Is MD5 still secure for password hashing?
Answer: No, because MD5 is susceptible to brute-force, rainbow table, and collision attacks, it is no longer secure for password hashing. For password security, consider more recent options like SHA-256, Argon2, or bcrypt.
Q2. Why is MD5 still used if it is not secure?
Answer: In applications where speed and efficiency are more important than cryptographic security, like file integrity verification, checksums, and digital forensics, MD5 is still utilized.
Q3. How does MD5 ensure data integrity?
Answer: From any input, MD5 creates a 128-bit hash that serves as a distinct fingerprint. It is helpful for file verification and checksums since the hash produced will be entirely different if the data is changed, even by a single bit.
Q4. Can two different inputs produce the same MD5 hash?
Answer: Yes, when two distinct inputs produce the same hash value, it’s known as a collision attack. Because of this flaw, MD5 is inappropriate for cryptographic uses such as authentication and digital signatures.
Q5. What are the best alternatives to MD5?
Answer: Better defenses against collisions and brute-force assaults are provided by more secure options like SHA-256, SHA-3, bcrypt, and Argon2. These techniques are suggested for password hashing and cryptographic security.