What is ElGamal Encryption Algorithm?
An asymmetric cryptographic technique for safe data transfer is the ElGamal Encryption Algorithm. It works on the discrete logarithm issue, which is computationally challenging to answer, and modular arithmetic. It is based on the Diffie–Hellman key exchange. In ElGamal, a pair of keys is used:
- A public key for encryption
- A private key for decryption
Randomized encryption, which produces distinct ciphertexts when the same communication is encrypted several times, is one of its primary characteristics. This strengthens its defenses against specific cryptographic threats and offers another degree of protection.
ElGamal serves as the foundation for a number of digital signature techniques and is extensively utilized in cryptographic systems that demand confidentiality, authentication, and integrity.
Introduction of ElGamal Encryption Algorithm
In 1985, renowned cryptographer Taher Elgamal unveiled the ElGamal Encryption Algorithm. It is a public-key cryptosystem that is useful in contemporary cryptography since it offers both digital signatures and encryption. The Discrete Logarithm Problem (DLP) in a finite cyclic group, usually found in modular arithmetic over a big prime number, serves as the mathematical basis for ElGamal. The algorithm’s security is guaranteed by the difficulty of addressing this challenge. Key characteristics of ElGamal include:
- Asymmetric structure: Uses a public key for encryption and a private key for decryption.
- Randomization: Each encryption uses a random value, ensuring that even if the same plaintext is encrypted multiple times, the ciphertexts are different.
- Semantic security: Prevents attackers from inferring information from ciphertext alone.
ElGamal serves as the foundation for a number of digital signature methods and is frequently utilized in secure communications, including Pretty Good Privacy (PGP). It is a dependable option for protecting sensitive data in contemporary cryptographic applications because of its emphasis on both confidentiality and unpredictability.
Detailed ElGamal Encryption Algorithm
The three primary stages of the ElGamal encryption algorithm are key generation, encryption, and decryption. It offers asymmetric encryption and uses a modular arithmetic approach.
A. Key Generation (Performed by the Receiver)
This step is done once to set up the system and generate public/private keys.
- Choose a large prime number p.
- Select a primitive root g modulo p.
- g is a generator of the multiplicative group modulo p.
- Select a private key x, such that 1<x<p−1.
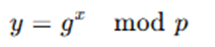
- Compute the public key component y:
Output,
- Public key: (p,g,y)
- Private key: x
B. Encryption (Performed by the Sender)
To encrypt a message m using the receiver’s public key (p,g,y):
- Ensure the message m is an integer such that m<pm <p. If not, break it into blocks.
- Choose a random number k such that 1<k<p−1.
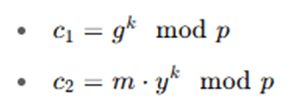
- Compute the two parts of the ciphertext:
Output:
- Ciphertext: (c1,c2)
The random value k ensures that encrypting the same message twice results in different ciphertexts.
C. Decryption (Performed by the Receiver)
To decrypt the ciphertext (c1,c2) using the private key x:
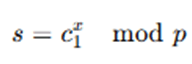
- Compute the shared secret:
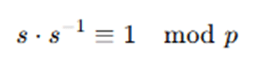
- Find the modular inverse of s, denoted s−1, such that:
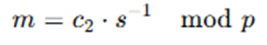
- Recover the plaintext message:
Explanation:
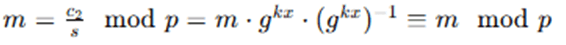
Since
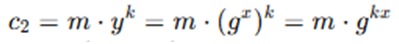
and
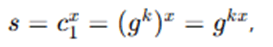
we get:
Example (Simplified with small numbers):
Let:
- p=23,
- g=5,
- Private key x=6
- Compute y=gx mod p=56 mod 23=8
Public key: (23,5,8)
Private key: x=6
Encrypt message m=13
Choose random k=10
- c1=510mod 23=9
- c2=13⋅810mod 23=13⋅16mod 23=208mod 23=1
- Ciphertext: (9,1)
Decrypt ciphertext (9,1)(9, 1)(9,1)
- s=96mod 23=16
- s−1=16−1mod 23=13
- m=1⋅13mod 23=13
Recovered message: 13
The ElGamal encryption algorithm follows a well-structured sequence of steps that includes key generation, encryption, and decryption. The process begins with key generation, where the receiver (who wants to receive encrypted messages) selects a large prime number p and a primitive root g modulo p. Then, a private key x is chosen randomly such that 1<x<p−1. Using this private key, the public key component y is calculated as y=gx mod p. The public key, which consists of (p,g,y), is shared openly, while the private key x is kept secret.
Once the public key is available, the sender can proceed to encrypt a message. To do this, the sender first ensures that the plaintext message m is an integer less than p; if the message is too large, it may need to be broken into smaller blocks. The sender then chooses a random integer k, which must also satisfy 1<k<p−1, and computes two values: c1=gk mod p and c2=m⋅yk mod p . These two values form the ciphertext pair (C1,C2), which is sent to the receiver. This use of a random value k in every encryption ensures that encrypting the same message multiple times will yield different ciphertexts, enhancing security.
To decrypt the ciphertext, the receiver uses their private key x to compute a shared secret s=c1x mod p. Since C1=gk , and x is the private key, s becomes gxg, which is also embedded in the ciphertext. The receiver then computes the modular inverse of s, denoted as s−1, and recovers the original plaintext message using the formula m=c2⋅s−1mod p. This decryption works because c2 contains the original message multiplied by s, and multiplying it by s−1 effectively cancels out the encryption, retrieving the original message. Thus, ElGamal achieves secure communication through mathematical operations grounded in number theory, particularly modular arithmetic and the discrete logarithm problem.
Advantages and Limitations of ElGamal Encryption Algorithm
Advantages
- Strong Security: Based on the Discrete Logarithm Problem (DLP), which is computationally hard to reverse, providing robust encryption security.
- Randomized Encryption: Uses a random value in each encryption process, ensuring that the same plaintext produces different ciphertexts each time, enhancing semantic security.
- Asymmetric Key System: Public and private keys are separate, enabling secure communication without sharing secret keys.
- Digital Signature Support: The algorithm can be adapted for digital signature generation and verification, making it versatile.
- Well-Studied and Proven: ElGamal has been thoroughly analyzed and is implemented in tools like PGP, GPG, and cryptographic protocols.
Limitations
- Ciphertext Expansion: ElGamal generates ciphertext that is twice the size of the plaintext, which increases storage and transmission requirements.
- Computational Overhead: Requires modular exponentiation and computation of modular inverses, making it slower compared to some symmetric or even asymmetric algorithms like RSA.
- Message Size Restriction: The plaintext message must be smaller than the prime number p, which may require splitting large messages into blocks.
- Random Number Dependency: The security heavily depends on the quality of the random number k. Weak or reused randomness can compromise encryption.
- Not Deterministic: While randomization increases security, it makes the algorithm less predictable and harder to test or verify in controlled environments.
Applications of ElGamal Encryption Algorithm
ElGamal encryption is widely used in cryptographic systems where data confidentiality, integrity, and authentication are critical. Its ability to provide both encryption and digital signatures makes it suitable for a range of applications.
- Secure Email Communication (PGP/GPG): ElGamal is used to provide encrypted email and file protection in Pretty Good Privacy (PGP) and GNU Privacy Guard (GPG). guarantees that the message can only be read and decrypted by the designated recipient.
- The ElGamal Digital Signature: Scheme is based on digital signatures. influenced the creation of the U.S. Digital Signature Standard (DSS), which includes the Digital Signature Algorithm (DSA). used to authenticate the sender and check the integrity of the communication.
- Electronic Voting Systems: Used in safe electronic voting procedures to protect voter confidentiality and stop fraud. supports voting processes that are anonymous and verifiable.
- Secure Communication and Messaging Protocols: Integrated into a number of cryptographic libraries and protocols for data transmission and secure messaging. used when message authenticity and confidentiality are necessary.
- Financial and Government Systems: Used in communication systems used by the government, military, and banks where strong public-key encryption is crucial.
Conclusion
A mainstay of contemporary public-key cryptography, the ElGamal Encryption Algorithm relies on the discrete logarithm issue to provide strong security. This technique, which was created by Taher Elgamal, provided a strong asymmetric encryption system that allowed for safe data transfer without the use of shared secret keys. Its randomized encryption method, which generates distinct ciphertexts for identical plaintext, enhances semantic security and provides a substantial defense against cryptanalytic assaults.Additionally, ElGamal is essential to electronic voting, digital authentication, and secure email systems due to its versatility in offering both encryption and digital signatures. Its demonstrated security and adaptability continue to make it a popular option in a variety of cryptographic applications, despite its higher processing requirements and bigger ciphertext size when compared to some competing algorithms. Algorithms such as ElGamal continue to play a crucial role in protecting integrity and privacy as digital communication becomes more important.
Frequently Asked Questions (FAQs)
1. What is the core security principle behind the ElGamal Encryption Algorithm?
The foundation of ElGamal’s security is the Discrete Logarithm Problem (DLP), which is practically impossible to deduce the private key from the public key due to its computational difficulty.
2. Why does ElGamal produce different ciphertexts for the same plaintext?
In order to improve security through randomized encryption, ElGamal employs a random value (k) in each encryption, guaranteeing that encrypting the same message more than once produces distinct ciphertexts.
3. Is ElGamal used in real-world cryptographic applications?
Indeed, ElGamal is extensively utilized in secure communication protocols, digital signatures, electronic voting, and systems like PGP (Pretty Good Privacy) and GPG.
4. How does ElGamal compare to RSA in terms of encryption?
Although both methods are asymmetric, ElGamal is more safe against some assaults since it provides randomized encryption. In contrast to RSA, ElGamal often generates longer ciphertexts and may execute more slowly in some cases.
5. Can ElGamal be used for digital signatures as well as encryption?
The Digital Signature Algorithm (DSA), which is commonly used in secure communications, is theoretically based on ElGamal, which can indeed be modified for digital signatures.