What is Elliptic Curve Cryptography (ECC) Algorithm?
Using the mathematical characteristics of elliptic curves over finite fields, Elliptic Curve Cryptography (ECC) is a public key cryptography technology that offers safe and effective digital signatures, key exchange, and encryption. ECC is based on the algebraic structure of elliptic curves defined by equations of the form:
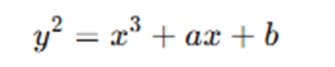
Where a and b are constants that define the curve, and the operations are performed over a finite field (typically a prime field Fp or a binary field F2m).
Key Characteristics of ECC are:
- Public key system: ECC employs a pair of keys, similar to RSA and DSA: a private key for decryption and signing, and a public key for encryption and verification.
- High security at modest key sizes: For instance, a 3072-bit RSA key and a 256-bit ECC key offer similar protection.
- Efficiency: Because ECC uses smaller keys, it uses less memory, bandwidth, and processing power, which makes it ideal for embedded systems, mobile devices, and the Internet of Things.
In ECC is a modern, compact, and secure cryptographic algorithm widely used in secure communications, digital identity, and blockchain systems.
Introduction of ECC Algorithm
Using the mathematics of elliptic curves over finite fields, Elliptic Curve Cryptography (ECC) is a contemporary public-key cryptography technique that offers robust security with lower key sizes. ECC was created as an alternative to more conventional algorithms like RSA and DSA, which need far larger keys to provide the same level of security, and was independently introduced by Victor Miller and Neal Koblitz in 1985.
Why ECC?
The increasing demand for safe communication, particularly in resource-constrained settings like smart cards, IoT systems, and mobile devices, necessitated the development of a robust and lightweight cryptographic technique. ECC responds to this requirement by:
- High encryption strength is provided, computational cost is decreased, and battery and bandwidth resources are preserved.
ECC is based on elliptic curves, which are defined by equations of the form:
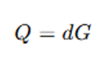
In order to construct cryptographic systems, these curves create an algebraic structure that facilitates operations like scalar multiplication and point addition. The foundation of ECC’s security is the Elliptic Curve Discrete Logarithm Problem (ECDLP), which is the challenge of determining d given Q=d.
ECC has been adopted by major standards bodies, including NIST, SECG, and ISO, and is used in:
- Secure web communications (TLS/SSL)
- Digital signatures (ECDSA)
- Cryptocurrency (e.g., Bitcoin and Ethereum)
- Secure messaging (e.g., Signal, WhatsApp)
In essence, ECC represents a powerful blend of security and performance, making it a preferred choice for modern cryptographic applications.
Detailed Explanation of ECC Algorithm
Elliptic Curve Cryptography (ECC) generates keys, encrypts data, and creates digital signatures by applying mathematical operations to elliptic curves. The ECC algorithm is explained in detail below, along with the important steps and pertinent calculations.
A. Elliptic Curve Equation
The general form of an elliptic curve over a finite field is:
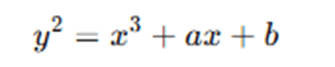
Where:
- a,b∈Fp
- p is a large prime number
- The curve must satisfy the condition 4a3+27b2≢0(modp) (to ensure it has no singularities)
B. Key Generation
- Select domain parameters:
- Prime number p
- Curve constants a, b
- Base point G=(xG,yG) on the curve
- Order n of the base point
- Private key:
- A random integer d∈[1,n−1]
- Public key:
- Q=dG (scalar multiplication of base point)
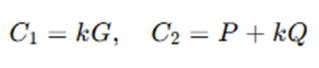
C. Encryption (Using ECIES – Elliptic Curve Integrated Encryption Scheme)
- Sender gets the recipient’s public key Q.
- Random integer k∈[1,n−1] is selected.
- Compute ephemeral keys:
- C1=kG
- C2=P+kQ, where P is the plaintext point mapped on the curve
- Send ciphertext (C1,C2)
Formulas:
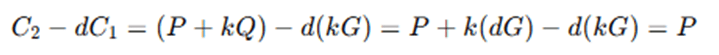
D. Decryption
Receiver uses private key d to compute:

Because:
E. Digital Signatures (ECDSA – Elliptic Curve Digital Signature Algorithm)
Signing Process:
- Choose a random integer k∈[1,n−1]
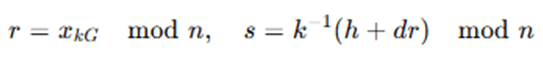
- Compute R=kGR, and take r=xR mod n
- Compute message hash h=Hash(m)
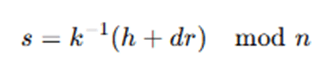
- Compute:
- Signature is (r,s)
Formulas:
Verification Process:
- Compute message hash h
- Compute:
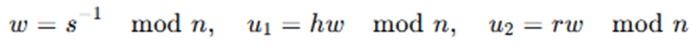
- Compute:
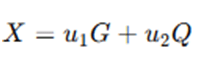
- Verify if r≡xX mod n
ECC Operations,
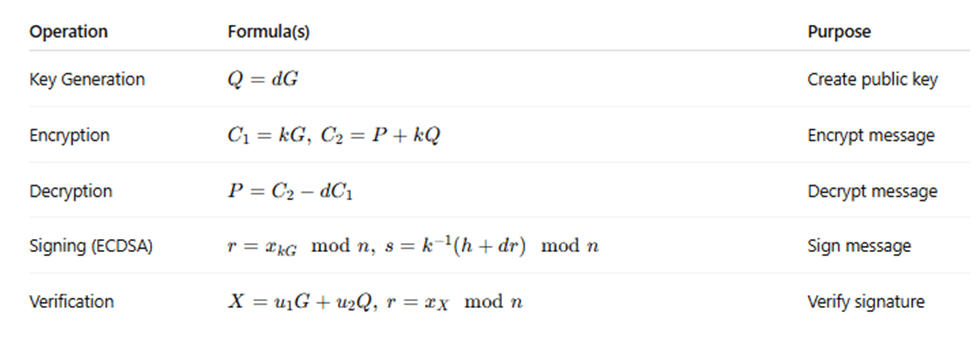
Elliptic Curve Cryptography (ECC) is a public-key encryption system that relies on the mathematics of elliptic curves over finite fields. The algorithm works by performing operations on points on an elliptic curve, which are defined by an equation of the form y2=x3+ax+b, where a and b are constants, and all calculations are performed within a finite field (usually a prime field Fp). The strength of ECC lies in the difficulty of the Elliptic Curve Discrete Logarithm Problem (ECDLP), which involves finding an integer d such that Q=dG, where G is a known base point and Q is the public key. The algorithm begins with key generation. A user first selects a set of domain parameters, which include the elliptic curve equation, a prime number p defining the finite field, a base point G on the curve, and the order n of the point G. The user then chooses a random private key d, where 1<d<n, and computes the corresponding public key Q=dG using scalar multiplication. For encryption, typically using the Elliptic Curve Integrated Encryption Scheme (ECIES), the sender uses the recipient’s public key Q. A random integer k is selected, and two points are calculated: C1=kG, and C2=P+kQ, where P is the plaintext point mapped onto the elliptic curve. The pair (C1,C2) is then transmitted as the ciphertext.
During decryption, the recipient uses their private key d to compute the original message point as P=C2−dC1. This works because dC1=dkG=kQ, and subtracting that from C2 cancels out the added component, recovering P.
ECC is also widely used for digital signatures, specifically through the Elliptic Curve Digital Signature Algorithm (ECDSA). In the signing process, the sender computes a hash h of the message and selects a random integer k. They then compute the point R=kG, take r=xR mod n, and compute s=k−1(h+dr)mod n. The signature consists of the pair (r,s). To verify the signature, the receiver calculates w=s−1mod n, then u1=hw mod n and u2=rwmod n The point X=u1G+u2Q is then computed, and the signature is valid if r≡xXmod n. In essence, ECC provides a secure framework for cryptographic operations by leveraging elliptic curve mathematics, enabling strong encryption, efficient key exchange, and compact digital signatures with lower resource usage compared to traditional methods like RSA.
Advantages and Limitations of ECC Algorithm
Advantages of ECC:
- Strong Security with Smaller Key Sizes: ECC provides high levels of cryptographic strength with much shorter keys compared to RSA and other classical algorithms. For instance, a 256-bit ECC key offers comparable security to a 3072-bit RSA key, making it more efficient.
- Faster Computation: Due to its smaller key sizes, ECC enables faster encryption, decryption, digital signature generation, and verification processes. This reduces computational time and energy consumption.
- Lower Resource Consumption: ECC is ideal for environments with limited processing power, memory, and bandwidth, such as mobile devices, IoT devices, and embedded systems.
- Efficient Bandwidth Usage: Smaller key and signature sizes mean less data is transmitted over the network, improving performance in communication-heavy applications.
- Wide Adoption and Standardization: ECC is supported by major security protocols (TLS/SSL, SSH, PGP), operating systems, and cryptographic libraries, and is standardized by organizations like NIST and IEEE.
Limitations of ECC:
- Complex Implementation: The mathematics behind ECC is more complex than that of RSA or AES, making secure and bug-free implementation more difficult and error-prone.
- Patent and Licensing Issues (Historical): Earlier adoption of ECC was hindered by patents, although most have now expired. Still, concerns over intellectual property once slowed its acceptance.
- Vulnerability to Side-Channel Attacks: Like all cryptographic algorithms, ECC implementations can be vulnerable to side-channel attacks (e.g., timing or power analysis) if not properly secured.
- Not Quantum-Resistant: ECC is susceptible to quantum computing attacks. Shor’s algorithm, when run on a sufficiently powerful quantum computer, could break ECC encryption, making it unsuitable for long-term security in a post-quantum world.
- Point Mapping Challenges in Encryption: In schemes like ECIES, plaintext must be mapped to a point on the elliptic curve, which can be non-trivial and requires additional cryptographic techniques to handle properly.
Applications of Elliptic Curve Cryptography (ECC) Algorithm
Because it may provide great security with minimal computing overhead, Elliptic Curve Cryptography (ECC) is widely used in many different fields. The use of ECC in protocols like TLS/SSL to create encrypted connections between web servers and clients is one of the most well-known applications in secure internet communications. ECC-based certificates, like ECDSA, are used by popular websites and browsers to offer secure HTTPS connections with reduced resource consumption and faster load times.
Blockchain technology and cryptocurrency both make extensive use of ECC. For example, ECC—more especially, the secp256k1 curve—is used by Bitcoin and Ethereum to generate wallet addresses, sign transactions, and confirm ownership. This makes it possible to handle digital assets and decentralized apps securely and effectively. Because of its lightweight design, ECC is the recommended option in the realm of embedded and mobile security. ECC is incorporated into the encryption and authentication processes of mobile operating systems such as iOS and Android, guaranteeing safe communication, messaging, and storage even on low-processing-power devices. ECC is also used in RFID systems, smart cards, and Internet of Things (IoT) devices, where small key sizes and low power consumption are crucial. ECC is also essential for digital signatures and authentication, especially for software code signing, electronic documents, and secure email (S/MIME, PGP). All things considered, ECC is a flexible cryptographic tool that supports several vital security applications in sectors like banking, healthcare, defense, and telecommunications, making it a crucial part of contemporary cybersecurity infrastructure.
Conclusion
One of the most effective and safe public-key cryptography methods now in use is Elliptic Curve Cryptography (ECC). Compared to more conventional techniques like RSA or DSA, ECC achieves high levels of security with substantially smaller key sizes by leveraging the intricate mathematical features of elliptic curves over finite fields. Because of this, ECC is especially useful in settings with constrained processing power, memory, and bandwidth, such embedded applications, mobile devices, and Internet of Things systems.
The Elliptic Curve Discrete Logarithm Problem’s (ECDLP) difficulty, which offers a strong basis for encryption, digital signatures, and safe key exchange, is the algorithm’s strength. Faster cryptographic operations while upholding high security standards are made possible by its small and computationally efficient design.
In conclusion, ECC is an essential instrument in the rapidly changing field of digital security because it provides a convincing balance between protection and performance. In a wide range of contemporary technologies, ECC will remain essential for protecting data, communications, and digital identities as the need for strong yet lightweight cryptographic solutions increases.
Frequently Asked Questions (FAQs)
Q1: Why is ECC preferred over RSA in modern cryptography?
Answer: ECC is perfect for mobile and embedded systems because it offers the same level of security as RSA with significantly smaller key sizes, resulting in faster calculations, lower battery consumption, and lower bandwidth utilization.
Q2: What is the main mathematical problem that ECC is based on?
Answer: The Elliptic Curve Discrete Logarithm Problem (ECDLP), on which ECC is built, is the process of determining an integer d given two points on an elliptic curve, G and Q=dG. The security of ECC is based on this computationally challenging problem.
Q3: Can ECC be used for both encryption and digital signatures?
Answer: Yes, both features are supported by ECC. Schemes like ECIES can be used for encryption, and algorithms like ECDSA (Elliptic Curve Digital Signature Algorithm) are used to implement digital signatures.
Q4: Is ECC secure against quantum computing?
Answer: No. ECC is susceptible to quantum assaults, particularly Shor’s algorithm, which has the potential to solve the ECDLP effectively, just like RSA and other classical cryptosystems. To counter this threat, post-quantum cryptography research is still in progress.
Q5: Where is ECC commonly used today?
Answer: ECC is commonly used in mobile OS encryption, smart cards, cryptocurrency wallets, TLS/SSL certificates, secure messaging apps (like Signal), and other security-sensitive applications where security and efficiency are crucial.