What is RSA Algorithm?
A public-key cryptography technique called Rivest–Shamir–Adleman (RSA) makes it possible to send data securely via unprotected networks. It employs two distinct keys, making it an asymmetric encryption technique are a public key for data encryption and a private key for data decryption. RSA bears the names of its creators, Leonard Adleman, Adi Shamir, and Ron Rivest, who first presented it at MIT in 1977. Key Concept of RSA is, while multiplying two large prime numbers together is simple, reversing the process, or factorizing the resultant large number, is computationally very challenging. The mathematical difficulty of factoring a large composite number into its two prime components is the foundation of RSA’s security. Thus, RSA provides a secure way to Encrypt confidential data, Authenticate digital information (digital signatures), and Establish secure connections over the internet.
Introduction of RSA Algorithm
RSA, or Rivest-Shamir-Adleman, is one of the oldest and most popular public-key cryptography techniques. RSA, which was first presented in 1977 by Ron Rivest, Adi Shamir, and Leonard Adleman, transformed secure communication by allowing two parties to safely exchange data without first disclosing a secret key. RSA operates on the principle of asymmetric encryption, where:
- The public key is openly shared and used to encrypt data.
- The private key is kept secret and used to decrypt data.
The power of the approach is found in the mathematical complexity of prime factorization: whereas multiplying two huge prime numbers together is simple, identifying the original primes from their result is quite challenging. Today, RSA is a fundamental technology used in:
- Secure web communications (SSL/TLS)
- Email encryption
- Digital signatures
- Cryptographic protocols like VPNs, cryptocurrencies, and secure file sharing.
Even now, RSA remains one of the most reliable cryptographic algorithms due to its extensive use and solid mathematical foundation, however alternative approaches are starting to emerge to supplement or even replace it in some situations.
Detailed RSA Algorithm
The RSA algorithm operates in three major phases:
Key Generation, Encryption, and Decryption.
Step 1: Key Generation
Goal: Generate a public key and a private key.
1.1 Choose Two Large Prime Numbers
- Select two distinct large prime numbers:

1.2 Compute the Modulus n
- Multiply p and q:
- n is used as part of both the public and private keys.
1.3 Compute Euler’s Totient Function φ(n)
- Calculate:

- This value is used to ensure the keys work correctly.
1.4 Choose the Public Exponent e
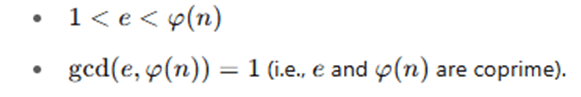
- Select an integer e such that:
1.5 Compute the Private Exponent ddd
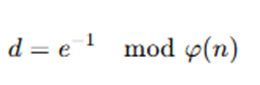
- Calculate d as the modular multiplicative inverse of e modulo φ(n):
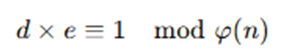
- d satisfies:
Final Keys:
- Public Key: (e,n)
- Private Key: (d,n)
Step 2: Encryption
Goal: Encrypt a plaintext message M using the public key (e,n).
- The plaintext message M must be an integer such that 0≤M<n.
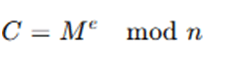
- Compute the ciphertext C using the formula:
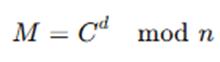
Step 3: Decryption
Goal: Decrypt the ciphertext C back to the original message M using the private key (d,n).
- Compute the plaintext message M using the formula:
Quick Example:
(Using small numbers for illustration only — not secure in real applications)
- Choose p=61p, q=53
- n=61×53=3233
- φ(n)=(61−1)(53−1)=3120
- Choose e=17 (17 and 3120 are coprime)
- Compute d such that d×17≡1mod 3120
(we find d=2753)
Public key: (e=17,n=3233)
Private key: (d=2753,n=3233)
Suppose we want to encrypt message M=65:
- Encryption:
- Decryption:
The Rivest–Shamir–Adleman (RSA) algorithm is a public-key cryptographic system that functions through three major phases: key generation, encryption, and decryption. The first step is key generation, where two large prime numbers, typically denoted as p and q, are selected. These primes are multiplied to obtain n=p×q, which forms part of both the public and private keys. Next, Euler’s totient function φ(n)=(p−1)(q−1) is computed. After that, a public exponent eee is chosen such that it is relatively prime to φ(n), meaning gcd(e,φ(n))=1. The private exponent d is then calculated as the modular multiplicative inverse of e modulo φ(n), satisfying the equation d×e≡1mod φ(n). At this stage, the public key is composed of (e,n), and the private key is (d,n).
Once the keys are generated, the encryption process begins. To encrypt a message M, the sender uses the recipient’s public key (e,n) and computes the ciphertext C using the formula C=Me mod n. The ciphertext C can then be transmitted securely. Upon receiving the ciphertext, the recipient uses their private key (d,n) to decrypt the message by computing M=Cd mod n, thereby recovering the original plaintext message. The RSA algorithm ensures that only the private key holder can decrypt the message, even though the encryption key is public. The algorithm’s strength lies in the mathematical difficulty of factoring the large number n back into its prime components p and q, which is currently considered computationally infeasible with classical computers. This makes RSA highly effective for secure data transmission, digital signatures, and cryptographic key exchanges.
Advantages and Limitations of RSA Algorithm
Advantages
- Strong Security: The foundation of RSA is the mathematical challenge of factoring huge prime numbers, a problem for which there isn’t yet an effective answer. When the right key lengths are utilized, this makes it extremely secure.
- Asymmetric Key System: RSA employs a public and private key pair, enabling secure communication without requiring the prior exchange of secret keys. This makes safe key sharing across public networks easier.
- Facilitates Digital Signatures: RSA facilitates the use of digital signatures in addition to encryption, offering non-repudiation, data integrity, and authentication.
- Broad Adoption and Proven Reliability: RSA is widely used in contemporary security protocols including SSL/TLS, digital certificates, VPNs, and email encryption. It has undergone thorough testing.
- Scalable Security: RSA can be made more secure by increasing the key size, allowing adaptability to evolving security threats.
Limitations
- Slower Performance: Compared to symmetric encryption techniques like AES, RSA requires more computing power and operates more slowly. For encrypting vast amounts of data, it is ineffective.
- Large Key Sizes Needed: RSA requires large key sizes (2048 bits or more) to maintain security, which raises the computational load and could impact performance in contexts with limited resources.
- Unsuitable for Encrypting Large Data Sets: RSA is usually used to encrypt tiny data, such as symmetric session keys, rather than big datasets because of its slow processing performance.
- Open to Quantum Attacks: Shor’s technique, which can factor big numbers effectively, could be used by quantum computers to crack RSA. This poses a serious risk in the long run.
- Complex Key Management: While RSA simplifies key distribution compared to symmetric systems, managing and securing private keys, especially in large systems, still requires careful planning and infrastructure.
Applications of RSA Algorithm
- The RSA algorithm is frequently used in many different sectors where data integrity and secure communication are essential. One of its most popular applications is secure web browsing, where it facilitates the creation of encrypted connections using protocols like SSL/TLS, guaranteeing secure online transactions.
- RSA is also crucial to email security, providing email encryption and digital signatures that authenticate the legitimacy of the sender and prevent manipulation.
- RSA is used to safely exchange encryption keys in the context of Virtual Private Networks (VPNs), safeguarding data while it moves over public networks.
- RSA is frequently used by blockchain systems and cryptocurrency platforms for user identification, transaction signing, and secure key management.
- Furthermore, RSA is essential to software distribution since it guarantees that downloads and updates are authentic and unaltered by malevolent actors. RSA is a fundamental technology in many security systems across industries due to its adaptability in both encryption and authentication.
Conclusion
Today, one of the most significant and enduring cryptographic systems is the Rivest–Shamir–Adleman (RSA) algorithm. By facilitating secure communication over public networks without the need for secret key exchange, its launch represented a significant advancement. RSA offers a strong basis for digital signatures and encryption, based on the mathematical difficulty of factoring big prime numbers. Even with the advent of more advanced cryptographic techniques, RSA is still widely used and trusted in a variety of sectors, including digital finance and safe web browsing. For the foreseeable future, RSA will continue to be a crucial part of cybersecurity due to its demonstrated security, adaptation to bigger key sizes, and versatility. However, recent developments in computing, particularly quantum computing, underscore the necessity for ongoing innovation in cryptography.
Frequently Asked Questions (FAQs)
Q1. Why is RSA considered secure?
Answer: The difficulty of factoring extremely big integers into prime factors is the foundation of RSA’s security. While multiplying two large primes together is simple, factoring—the opposite of multiplication—is computationally impossible with current technology, particularly for keys with 2048 bits or more.
Q2. What happens if someone factors the modulus n?
Answer: An attacker can calculate the private key d from the public key if they can factor nnn into its prime components, p and q. They would be able to decipher all messages encrypted with that key since this would totally undermine the RSA system’s security.
Q3. How large should RSA keys be to remain secure?
Answer: For general security, a minimum key size of 2048 bits is currently advised. 3072-bit or 4096-bit keys are frequently utilized for applications requiring enhanced security. Stronger security (but with more computing effort) results from greater key sizes.
Q4. Is RSA vulnerable to quantum computers?
Answer: In theory, yes. RSA could be broken using quantum algorithms that factor big numbers rapidly, such as Shor’s algorithm. But there are currently no quantum computers strong enough to accomplish this. Post-quantum cryptography is being studied by numerous organizations as a future-proof substitute.
Q5. Can RSA be used for encrypting large data?
Answer: No, RSA is ineffective when dealing with big datasets. Usually, a small symmetric key (such as AES) is encrypted first, and the actual massive data is subsequently encrypted. The advantages of both symmetric and asymmetric encryption are combined in this hybrid method.