The topic of quantum cyber security is going through a radical change as scalable quantum computers become a reality. The computational dominance of quantum computing poses an immediate danger to traditional cybersecurity paradigms, necessitating the development of quantum-resilient cryptographic algorithms and security frameworks. 2025 offers research researchers a pivotal moment: an opportunity to support fundamental studies that may protect digital communications in the post-quantum age. This thorough paper examines the main topics of quantum cyber security research that academics ought to focus on in 2025. Technical depth, practical relevance, and conformity to contemporary academic and industrial trends are prioritized.
Post-Quantum Cryptography (PQC)
Lattice-Based Cryptography
Lattice-based encryption has emerged as a leading candidate in the realm of post-quantum cryptography research due to its strong worst-case hardness assumptions and resistance to both classical and quantum computational attacks. Schemes like Learning With Errors (LWE), Ring-LWE, and Module-LWE offer mathematically sound foundations on which key encapsulation mechanisms (KEMs) and digital signature algorithms, many of which are advancing through the National Institute of Standards and Technology (NIST) standardization process, can be constructed. The optimization of key generation and signature procedures in lattice-based schemes is a crucial field of study, particularly as practical implementations demand balancing the demands of bandwidth, computing efficiency, and security level.
Code-Based and Multivariate Cryptography
Lattice-based constructions currently dominate the post-quantum cryptography landscape, but alternative paradigms such as code-based and multivariate public key cryptosystems remain crucial for ensuring algorithmic variety and safeguarding against future developments in cryptanalysis. Code-based encryption, such as the McEliece cryptosystem, has a solid security history and is resistant to quantum adversaries because random linear codes are hard to decipher, a task that is believed to be impossible even for quantum computers. To solve problems like large public key sizes, parameter tuning, code selection (e.g., MDPC codes, Goppa codes), and implementation efficiency, more study is required. However, multivariate polynomial-based cryptosystems take use of the NP-hardness of solving systems of multivariate quadratic equations over finite fields. Therefore, it is becoming increasingly vital to conduct research on building secure implementations that minimize information leakage and incorporate countermeasures like masking, blinding, and fault detection techniques. Collectively, these efforts contribute to the diversification and reinforcement of the post-quantum cryptography landscape.
Quantum Key Distribution (QKD)
QKD leverages the principles of quantum mechanics, particularly the no-cloning theorem and Heisenberg uncertainty, to establish provably secure communication channels.
QKD Protocol Development
Secure quantum communication is based on Quantum Key Distribution (QKD) protocols as BB84, E91, and Measurement-Device Independent QKD (MDI-QKD). The confidentiality of distributed keys is guaranteed by these protocols, which use quantum concepts, although their actual implementation necessitates considerable improvements.
Finite-key analysis, which evaluates protocol security in scenarios with constrained key lengths, is an important area of study. Finite-size analyses, as opposed to asymptotic security models, need tight, composable security proofs under practical restrictions since they have to take statistical fluctuations, noise, and device flaws into consideration.
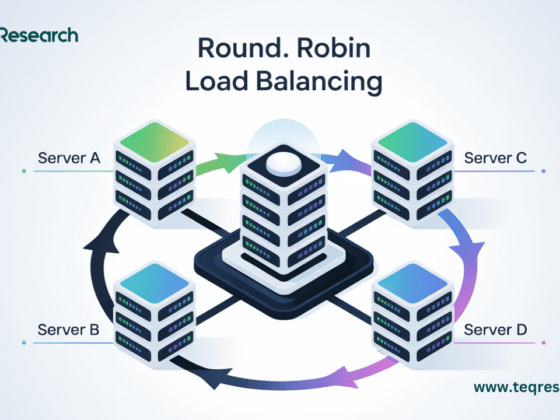
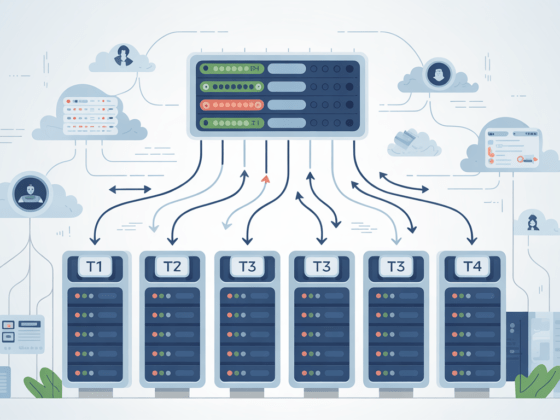
Another significant issue is protocol scalability, especially when incorporating QKD into traditional network architectures. This entails regulating optical loss across urban distances, modifying protocols for multi-user environments, and guaranteeing interoperability with software-defined networking (SDN) infrastructures.
Lastly, the creation of device-independent QKD (DI-QKD) is essential for reducing vulnerabilities brought on by faulty or unreliable hardware. By using nonlocal quantum correlations and Bell test violations, DI-QKD techniques validate security without relying on assumptions about how devices operate internally.
Quantum Repeaters and Network Scalability
Photon loss and decoherence in optical fibers are fundamentally limiting factors for long-distance QKD. By facilitating entanglement distribution across long distances via entanglement swapping and purification, quantum repeaters are crucial for overcoming this distance barrier. Error-correcting quantum memories that can store entangled states with long coherence periods and low operational error rates are necessary for the implementation of functional repeaters. These memories need to provide synchronization with entangled photon sources and be compatible with photonic interfaces.
Maintaining entanglement fidelity across noisy channels is another difficulty when establishing entanglement over long distances. To manage entanglement swapping activities across multi-node networks and create fault-tolerant entanglement distribution methods, more research is required. Efficient synchronization and routing within quantum networks is critical for scalable QKD. This includes precise timing coordination, clock distribution mechanisms, and adaptive routing algorithms that account for quantum channel availability and noise dynamics.
Quantum-Safe Blockchain and Distributed Ledger Technologies
Traditional public-key cryptography techniques like RSA and the Elliptic Curve Digital Signature Algorithm (ECDSA) are crucial to the security and integrity of contemporary blockchain ecosystems. These algorithms serve as the foundation for consensus and transaction authentication systems, but they are intrinsically susceptible to quantum attacks, especially through Shor’s algorithm, which allows for discrete logarithm calculations and effective factorization on a strong enough quantum computer. Because it would enable quantum attackers to alter historical records, forge signatures, and compromise user credentials, this vulnerability presents an existential threat to digital ledgers.
The incorporation of post-quantum cryptography (PQC) primitives is crucial for future-proofing blockchain systems. The creation and improvement of quantum-resistant digital signature systems that are especially suited to blockchain limitations, such as constrained block sizes, high throughput demands, and decentralized verification, constitutes one important research avenue. Although hash-based structures like SPHINCS+ and lattice-based methods like Dilithium have been developed, they still need to be improved upon to guarantee scalability and computational efficiency across various blockchain platforms.
At the same time, lightweight consensus techniques that are naturally resistant to adversaries with quantum capabilities are desperately needed. In the context of quantum speed-ups, conventional consensus techniques, especially proof-of-work (PoW), may become ineffective or unsafe. Developing hybrid consensus models or completely original systems that preserve Byzantine fault tolerance without depending on traditional cryptographic presumptions is the main goal of this field of study.
Last but not least, one of the most important aspects of blockchain security in the quantum age is the formal verification of quantum-safe smart contracts. Strict formal techniques are needed to guarantee that smart contracts—executable code that controls decentralized applications—remain safe under post-quantum assumptions. This involves the safe integration of PQC libraries into virtual machine environments, resistance to quantum-related vulnerabilities, and the use of model checking, theorem proving, and symbolic execution to ensure correctness.
Research directions:
- Design of post-quantum digital signature schemes for blockchain.
- Lightweight consensus protocols resistant to quantum adversaries.
- Formal verification of quantum-safe smart contracts.
Quantum Threat Modeling and Risk Assessment
Current cybersecurity frameworks still lack comprehensive threat models that explicitly take quantum computational capabilities into account. The revolutionary potential of quantum algorithms, like Shor’s and Grover’s, to radically challenge established cryptographic presumptions is frequently overlooked in traditional threat assessments. Establishing a quantum-aware risk assessment paradigm that methodically describes vulnerabilities resulting from both near-term and fault-tolerant quantum adversaries is imperative in order to close this gap. According to estimations of quantum resources, attack vectors unique to quantum-enhanced capabilities, and timetables for quantum breakthroughs, such a system ought to assess exposure levels. Organizations will be able to prioritize mitigation methods, direct the shift to quantum-resistant designs, and improve the resilience of critical infrastructure against quantum-enabled attacks by integrating this framework with current standards (such as NIST and ISO).
Key research tasks:
- Quantitative risk metrics incorporating quantum threat horizons.
- Simulation frameworks for quantum attack scenarios.
- Integration with NIST and ISO cybersecurity standards.
Quantum-Enhanced Cryptographic Primitives
Even though creating defenses against adversaries with quantum capabilities has been the field’s main focus, an increasing amount of research is looking into how inherent quantum resources might be used to significantly improve cryptographic security. This paradigm shift investigates the creation of cryptographic primitives that provide security guarantees not possible by classical methods by utilizing quantum phenomena including entanglement, superposition, and no-cloning. Examples include quantum-secure multiparty computation frameworks that take advantage of quantum communication channels to increase efficiency and robustness; quantum digital signatures that offer non-repudiation with information-theoretic security; and quantum bit commitment and oblivious transfer protocols that allow for secure multiparty computations with provable privacy. These quantum-enhanced protocols are a viable avenue for developing security primitives that not only resist quantum assaults but also use quantum mechanics to increase the level of cryptographic confidence. However, they require thorough theoretical development and experimental confirmation.
Examples include:
- Quantum digital signatures.
- Quantum bit commitment and oblivious transfer.
- Quantum-secure multiparty computation (MPC).
These protocols require rigorous theoretical development and experimentation.
Side-Channel Analysis and Fault Injection in PQC
Despite being built to withstand cryptanalytic attacks from quantum computers, post-quantum cryptography (PQC) systems are nevertheless vulnerable to physical attack vectors including fault injection and side-channel attacks. Unintentional information leakage due to timing discrepancies, power usage, electromagnetic emissions, or induced errors during cryptographic procedures is the source of these vulnerabilities. A dual analysis methodology that includes both classical and quantum-capable adversary models is necessary to evaluate the resilience of PQC algorithms. Sensitive key material may be extracted by quantum attackers using new quantum side-channel techniques or improved measurement techniques. Therefore, it is essential to create thorough leakage-resilient designs, formal leaking models, and automated evaluation methods. This includes developing simulation environments that mimic quantum-enhanced physical attack scenarios, implementing masking and hiding countermeasures suited for PQC primitives, and incorporating side-channel resistance into the algorithmic design phase. To guarantee that PQC implementations maintain strong security against the entire range of adversary capabilities in practical operational situations, these issues must be addressed.
Research interests:
- Modeling leakage-resilient PQC algorithms.
- Automated tools for side-channel resistance analysis.
- Integration of physical attack simulations into PQC design.
Quantum-Resilient Authentication Protocols
A key element of secure communication systems are authentication methods, which guarantee the validity of persons conversing and stop unwanted access. However, when faced with adversaries possessing quantum processing capabilities, traditional challenge-response mechanisms—which frequently rely on cryptographic primitives susceptible to quantum attacks (such as RSA, ECDSA)—face serious hazards. The underlying hard problems that ensure the security of these protocols can be effectively resolved by quantum algorithms like Shor’s algorithm, which may make impersonation and session hijacking possible. Therefore, in order to provide resistance to both classical and quantum attackers, it is important to build quantum-resilient authentication techniques that combine post-quantum cryptographic primitives. Developing protocols for authenticating quantum devices in heterogeneous Internet-of-things (IoT) ecosystems, integrating biometric or behavioral authentication with quantum-safe encryption, and modifying zero-knowledge proofs for PQC contexts are all promising research avenues. To protect future communication infrastructures from quantum-enabled threats, robust authentication systems must strike a balance between computing efficiency, security guarantees, and practical deployability.
Promising directions:
- Zero-knowledge proofs adapted for PQC settings.
- Biometric and behavioral authentication with quantum-safe cryptography.
- Protocols for quantum device authentication in IoT.
Secure Multi-Party Computation (SMPC) in a Post-Quantum World
In extremely sensitive fields like healthcare and finance, secure computing methods between parties that are skeptical of one another are essential for preserving data confidentiality and integrity. With the help of these protocols, several users can collaboratively calculate a function over their private inputs without disclosing any information other than the desired result. To provide resistance against adversaries with quantum computational capabilities, traditional secure multi-party computation (SMPC) systems need to be reassessed and modified to incorporate post-quantum cryptographic primitives in light of anticipated quantum threats. Building quantum-safe secret sharing methods, using lattice- or code-based cryptographic primitives for threshold cryptography, and maximizing communication efficiency to reduce the performance cost brought on by quantum-resistant algorithms are some of the main research problems. To ensure strong privacy and accuracy guarantees in quantum-aware SMPC protocols, formal security proofs must also cover adversaries that can carry out quantum attacks, such as adaptive and active adversaries. In order to enable collaborative decision-making and privacy-preserving data analytics in quantum-resilient distributed systems, these issues must be resolved.
Research opportunities:
- Designing PQC-based secret sharing schemes.
- Threshold cryptography using lattice-based primitives.
- Communication-efficient SMPC under quantum threat models.
Standardization and Policy Frameworks
The development of quantum-resistant cryptographic algorithms and protocols is making great strides, but in order to assure their safe and cogent adoption, regulations, regulatory frameworks, and standardization initiatives must all advance at the same time. In the quantum age, defining interoperability criteria, compliance benchmarks, and security validation techniques depends on technological improvements being in line with international standards, such as those set by NIST, ISO, and ETSI. To provide thorough recommendations that cover implementation issues, lifecycle management of quantum-safe technologies, and risk assessment procedures specific to quantum hazards, researchers and policymakers must work together. Furthermore, proactive regulatory frameworks are required to create certification procedures that verify quantum resilience, encourage industry use, and ease information sharing across sectors. By bridging the gap between theoretical research and real-world implementation, this integrated strategy will promote a safe environment that is resistant to present and future quantum attackers.
Scholars can contribute by:
- Developing testbeds for PQC integration.
- Analyzing regulatory compliance issues in quantum environments.
- Participating in standards bodies (e.g., IETF, ETSI, NIST).
Quantum-Resilient AI and Data Privacy
One new and extremely interesting area of study is the intersection of artificial intelligence (AI) and quantum cyber security. The integrity, privacy, and confidentiality of AI systems’ training datasets and decision-making pipelines become crucial security issues as they spread throughout a variety of industries, including healthcare and banking. In this context, quantum computing presents both opportunities and challenges. On the one hand, quantum adversaries may use sophisticated attacks, like model inversion or poisoning, accelerated by quantum algorithms, to take advantage of weaknesses in AI models. However, new methods for securing AI processes are provided by quantum-enhanced privacy-preserving protocols and quantum-resistant cryptography systems. Developing post-quantum encryption schemes to protect federated and distributed learning environments, incorporating differential privacy frameworks that are resilient to quantum threat models, and investigating quantum noise-based masking techniques to obscure sensitive data without impairing model performance are among the current research priorities. Maintaining reliable AI systems that can withstand the growing capabilities of attackers with quantum capabilities will require progress in several areas.
Cutting-edge research includes:
- Differential privacy in a quantum computing context.
- PQC-based encryption for federated learning.
- Privacy-preserving ML with quantum noise masking.
Conclusion
An effective, multidisciplinary strategy to cybersecurity is required in the upcoming quantum era. The aforementioned fields are important future infrastructures, not only theoretical quirks. By concentrating on these areas, researchers in 2025 can help create a more secure digital ecosystem in the face of quantum disruption.
Recommendations for Scholars:
- Align research with current NIST and ETSI quantum initiatives.
- Seek collaboration with quantum hardware and telecom industry leaders.
- Consider open-source contributions to PQC libraries and toolkits.
By investing in these key research areas in quantum cyber security, scholars will not only future-proof digital systems but also define the next era of secure computing.
Frequently Asked Questions (FAQs)
1. What is quantum cyber security and why is it important in 2025?
Creating cryptographic and security solutions that can withstand the power of quantum computing is the main goal of quantum cyber security. It is crucial to safeguard digital infrastructure from quantum threats as scalable quantum computers get closer to becoming a reality.
2. Which cryptographic techniques are most promising for post-quantum security?
For post-quantum encryption, the NIST standardization process revealed several top contenders, including multivariate polynomial schemes, code-based systems like McEliece, and lattice-based cryptography.
3. How does Quantum Key Distribution (QKD) enhance cybersecurity?
QKD ensures secure key exchange by utilizing quantum mechanical concepts. The state of quantum bits (qubits) is disturbed by any attempt to intercept them, making eavesdropping attempts visible.
4. Can blockchain technology be made quantum-resistant?
Yes, blockchain systems can be protected against quantum attacks by implementing consensus protocols and substituting post-quantum digital signatures for weak digital signatures like ECDSA.
5. What role can research scholars play in quantum cyber security?
By investigating novel cryptographic algorithms, assessing quantum threats, developing security protocols, and influencing standards and regulations that mold the post-quantum cybersecurity environment, academics can spur innovation.